What is Strict-Transport-Security?
The Strict-Transport-Security (HSTS) HTTP response header is a critical security mechanism used to enforce secure connections (HTTPS) between the browser and the server. It helps protect web applications from man-in-the-middle (MITM) attacks and protocol downgrade attacks by ensuring that all communication occurs over HTTPS.
How Strict-Transport-Security Works?
- When a browser receives an HTTP response with the Strict-Transport-Security header, it remembers the directive for a specified duration (max-age).
- For the specified duration, all subsequent requests to the server are automatically upgraded to HTTPS, even if the user enters http:// in the browser.
- The browser rejects any attempts to connect to the server using an insecure connection.
HSTS Header Syntax
The header is included in the HTTP response as:
HSTS Header Directives
- max-age: Specifies the duration (in seconds) for which the browser should enforce HTTPS.
For example: max-age=31536000 (1 year) - includeSubDomains (optional): Ensures HSTS is applied to all subdomains.
- preload (optional): Indicates the domain should be preloaded into browsers that maintain an HSTS preload list.
Benefits of HSTS
- Prevents Downgrade Attacks: Attackers cannot force a connection over HTTP by downgrading from HTTPS.
- Mitigates MITM Attacks: Ensures the connection is encrypted and authenticated.
- Improves User Trust: Guarantees that users access the website securely.
How to Implement HSTS
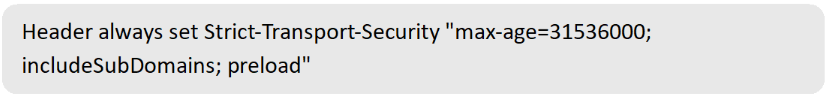
- Apache: Add the following line to the .htaccess file or server configuration
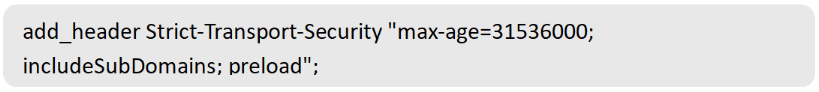
- Nginx: Add the following directive to your configuration file
- IIS: Configure the HTTP response headers to include
References
https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Strict-Transport-Security