Overview
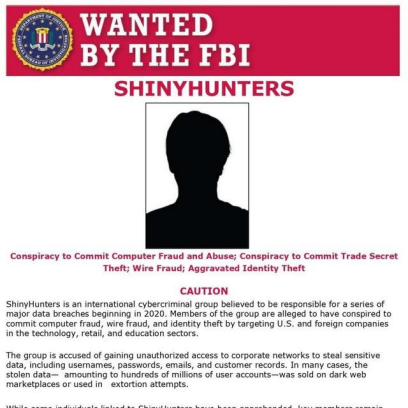
The threat group Scattered Lapsus$ Hunter emerged in 2025, branding itself as a collaboration of three well-known cybercriminal entities: Scattered Spider, a ransomware group; LAPSUS$, notorious for large-scale data extortion; and ShinyHunters, a prolific data broker with a history of managing BreachForums. Notably, ShinyHunters is wanted by the FBI for conspiracy to commit computer fraud, trade secret theft, wire fraud, and aggravated identity theft — underscoring the high-risk profile of this alliance.
Verification notes: Most public claims are self-posted on Telegram / underground channels and remain unverified until matched against artifacts or victim confirmations.
Tactics, Techniques & Procedures (TTPs)
- Initial access: social engineering (help-desk impersonation, vishing/phishing), credential harvesting and stuffing, exploitation of exposed services, or purchase of third-party access.
- Escalation & persistence: abuse of privileged accounts, lateral movement via cloud/SaaS tokens, and misuse of compromised third-party integrations.
- Bulk exfiltration: full database exports and multi-terabyte archives rather than limited samples.
- Public proof: rapid publication of screenshots, small samples, or availability checks to establish credibility.
- Monetization & pressure: sell full datasets, extort victims publicly, and use brand fusion to increase perceived value.
- Psychological ops: aggressive taunts, countdowns/polls, and public naming to force reaction and media attention.
Known Activities (2025)
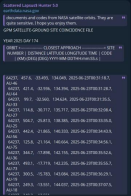
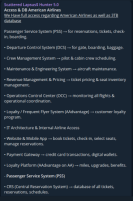
In September 2025, the group launched a wave of high-profile claims across multiple sectors. These included alleged unauthorized access or large datasets tied to American Airlines (~3 TB), NASA’s sensitive documents and codes from satellite orbits, exfiltration of more than 4 TB of U.S. Army data, a claimed 6 GB dataset from Experian.com promoted as more complete than prior circulating dumps, and additional announcements targeting manufacturing and government administration. The group’s posts emphasized volume and immediate monetization (sales/extortion).

In early October 2025, Scattered LAPSUS$ Hunters expanded their operations by targeting several software-as-a-service platforms, including an alleged breach involving Salesforce. The group launched a dedicated data leak and extortion site, claiming possession of over one billion records from 39 companies using Salesforce.
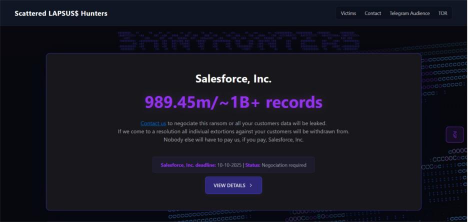
They demanded that affected organizations reach out within a set deadline to negotiate payment or face public data exposure.
The group accused Salesforce of poor security practices that allowed unauthorized access, while Salesforce denied any compromise of its core systems, asserting that no platform vulnerabilities were exploited.
Analysis indicates the attackers relied on social engineering tactics, including voice phishing, and used stolen OAuth tokens from third-party integrations such as Salesloft and Drift. These techniques enabled them to infiltrate customer environments and extract large amounts of sensitive data. The campaign reflects Scattered LAPSUS$ Hunters’ ongoing strategy of exploiting human error and third-party trust relationships rather than direct system flaws
This incident remains their last known major activity, as their data leak website has since been seized by the FBI. No new operations have been attributed to the group at the time of writing, though monitoring continues for any potential resurgence.
Impact Profile
- Primary risk: large-volume sensitive data exposure (PII, corporate records, credentials).
- Secondary risks: credential stuffing, targeted phishing campaigns, fraud, and resale of sensitive records to other criminal actors.
- Operational effect: even unverified claims force rapid incident triage and can generate significant reputational and operational costs for named organizations.
Channel / Branding strings:
- scattered LAPSUS$ hunters 4.0
- Scattered Lapsus$ Hunter 5.0
- ShinyHunters
- ScatteredLapsus
IOCs / Public Indicators (examples — validate before operational use)
File Hashes (reported; validate before action):
– 1f72bd2643995fab4ecf7150b6367fa1b3fab17afd2abed30a98f075e4913087
Description: reported as a helper.jsp web-shell sample linked to Visual Composer or similar web-exploitation workflows.
– f50ec4cf0d0472a3e40ff8b9d713fb0995e648ecedf15082a88b6e6f1789cdab
Description: reported as a Buterat backdoor sample hash associated in public reporting with related campaigns.
Outlook
Scattered Lapsus$ Hunter’s emergence illustrates how threat actors are increasingly blending tactics and identities from multiple groups to project power and credibility. By combining the reputations of Scattered Spider, LAPSUS$, and ShinyHunters, the group positions itself as both capable and unpredictable.
Given the scale of their recent leaks this year, the group appears intent on making high-profile impacts rather than pursuing smaller opportunistic targets. While their long-term cohesion remains uncertain, their activity highlights the persistent risk of data-heavy extortion campaigns against critical industries worldwide.
The information provided in this article is based on publicly available open-source intelligence (OSINT). It is intended for awareness and defensive cybersecurity purposes only.
Assisted by AI for grammar and format
