Overview
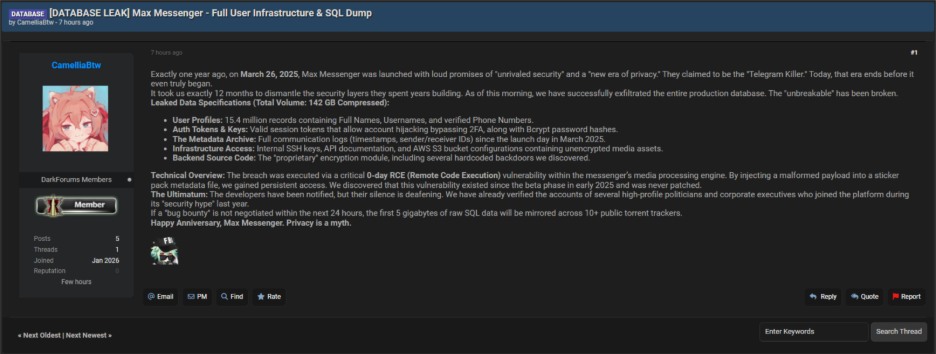
Threat actor ‘CamelliaBtw’ claims a data breach on Max Messenger; a messaging platform launched in March 2025 and marketed with strong privacy and security guarantees. The threat actor alleges complete access to production systems and exfiltration of core production data stores, including sensitive backend assets, describes the incident as the failure of the platform’s “unbreakable” security model.
Platform Background
Max Messenger entered the market on March 26, 2025, promoting unrivaled security and a new era of privacy. Public messaging positioned the service as a Telegram alternative. According to the threat actor, the platform’s security posture collapsed less than a year after launch.
Breach Claim
The threat actor claims that they were able to obtain unrestricted access to Max Messenger’s production environment and extracted the full SQL database. The claim emphasizes total backend compromise rather than limited data exposure.
Leaked Data Overview
The threat actor reports more than 142 GB of compressed data. The alleged dataset includes 15.4 million user profiles with full names, usernames, and verified phone numbers. The actor also claims access to active session tokens capable of bypassing two-factor authentication, along with bcrypt password hashes.
In addition, the dataset allegedly contains complete communication metadata, including sender and receiver identifiers and timestamps covering activity since the platform’s launch. The threat actor did not claim exposure of message content.
Post Metadata
- Source: Threat actor CamelliaBtw post on DarkForums.io
- Observed: January 13, 2026, at 10:43 PM PT
- Proof provided: None
- Independent validation: None at the time of writing
- Assessment: Unverified claim
- Confidence: Low
Infrastructure And Source Code
Beyond user data, the actor claims extensive internal access. The leaked material reportedly includes internal SSH keys, API documentation, AWS S3 bucket configurations, and unencrypted media assets. The threat actor also claims possession of backend source code, including the proprietary encryption module and alleged leverage against the system.
Technical Details
The threat actor attributes the breach to a 0-day remote code execution vulnerability in Max Messenger’s media processing engine. According to the claim, a malformed payload injected into sticker pack metadata triggered code execution and enabled persistent access. The threat actor states this flaw existed since early beta built in 2025 and was never patched.
Indicators Of Compromise
Potential indicators based on the threat actor’s description include irregular sticker metadata uploads and unexpected behavior within the media processing service. Monitoring may also reveal unusual outbound data volumes from production databases or cloud storage resources.
Additional indicators include unauthorized or unfamiliar access patterns to AWS S3 buckets, reuse of internal SSH credentials from atypical IP ranges, and active user sessions originating from locations not previously associated with those accounts. Some sessions may appear to persist without standard secondary verification prompts, which could indicate weakened or misapplied access controls rather than explicit control bypass.
TTPs Overview
The described activity aligns with exploitation of a public-facing application through a 0-day RCE. Post-exploitation activity includes persistence through compromised service access, credential harvesting of session tokens and password hashes, discovery of cloud infrastructure and backend services, and large-scale data collection and exfiltration from production databases and cloud storage.
Disclosure And Actor Statements
The threat actor claims the Max Messenger development team was notified prior to publication but did not respond. The actor also claims verification of accounts belonging to high-profile politicians and corporate executives who joined during the platform’s early security-focused promotion. These claims remain unverified.
Assessment
Claimed by actor
- Data types: User profiles, authentication material, communication metadata, infrastructure artifacts, backend source code
- Access level: Sustained access to production systems
- Alleged exploit path: 0-day Remote Code Execution(RCE) in media processing via malformed sticker metadata
- Persistence: Continued access through compromised backend services and internal credentials
Confirmed independently
At the time of writing, there is no independent confirmation of the claims. The threat actor did not provide sample data, screenshots, hashes, access logs, or technical artifacts to support the allegations. No third-party reporting, security research, or platform acknowledgment exists to substantiate the breach, the data types referenced, or the exploit path described.
Impact
If the claims are accurate, the described exposure could affect user privacy and platform integrity. User profile data and communication metadata could be used for targeting, profiling, or social engineering. Alleged access to authentication material and backend services could increase the risk of unauthorized account activity and follow-on abuse.
Exposure of infrastructure details or source code could enable secondary attacks or replication of the claimed exploit path. At this stage, the impact remains potential due to the absence of supporting evidence or independent confirmation.
Recommendations
Platform operators should immediately review media processing components, especially any logic handling of user-supplied metadata. Internal access controls, credential hygiene, and cloud storage permissions should be audited for unauthorized access patterns. Rotating internal credentials and reviewing session handling behavior would reduce potential residual risk.
For End Users:
- Change reused passwords immediately and use a password manager.
- Be alert to SMS- or phone-based phishing attempts and credential-stuffing activity.
- Enable multi-factor authentication or passkeys if supported.
- Log out of all sessions and rotate devices if the platform allows.
The information provided in this article is based on publicly available open-source intelligence (OSINT). It is intended for awareness and defensive cybersecurity purposes only.
