Summary
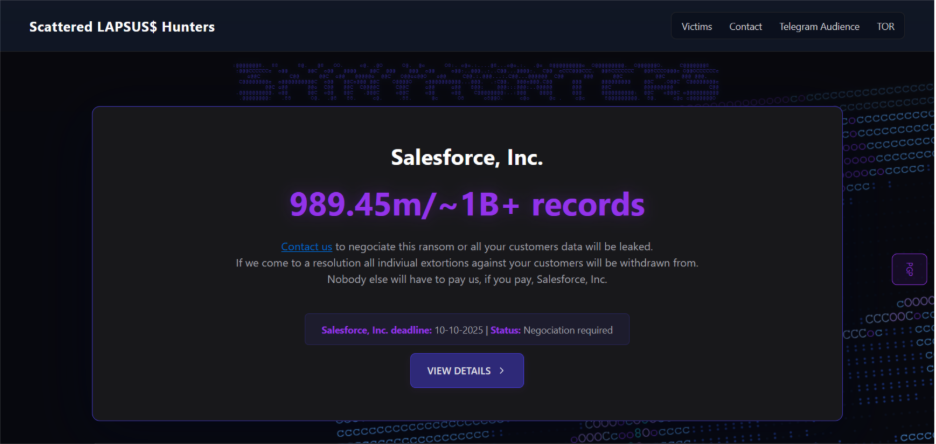
In late 2025 a group calling itself Scattered Lapsus$ Hunters posted an extortion note claiming responsibility for a major breach of Salesforce, Inc. The message asserts the exfiltration of allegedly “near 1 billion records” of sensitive PII, accuses Salesforce of weak security controls, threatens legal and public disclosure, and sets a ransom deadline. The posting offers no concrete technical proof (no file hashes, sample artifacts, domains or IPs) in the message itself — only an extortion narrative and a contact handle.
What the threat group claims
- Claimed exfiltration of nearly 1 billion records containing sensitive PII (driver licenses, DOBs, SSNs, etc.).
- Allegation that 100+ other instances were dumped due to weak OAuth/2FA controls.
- They threaten to provide lists, data samples, and to cooperate with law firms and media unless a ransom is paid.
- Deadline stated in the message (useful for timeline correlation): 10 Oct 2025 (formatted in the note as 10/10/25).
- Contact provided in the note (obfuscated): shinyc0rp[at]tuta[.]io.
- No technical artifacts (no hashes, no IPs, no download links) were included in the extortion note itself.
Assessment: the claim is high impact but currently unverified. The message is typical extortion rhetoric: large numbers, legal pressure, and reputational leverage. Without corroborating artifacts or telemetry, the message should be treated as a credible intelligence lead that requires immediate validation via internal logs and further OSINT monitoring.
Observable IoC (from the Compromised Data Overview)
- Contact / actor mail handle: shinyc0rp[at]tuta[.]io (obfuscated in the posting).
- Actor branding / channel type: references to an onion/dark-web posting by Scattered Lapsus$ Hunters.
- Deadline: 2025-10-10 (useful for triage/timeline).
Implied TTPs (behavioral summary) — mapped to MITRE ATT&CK
Below are the techniques the extortion note implies or references, with concise detection and mitigation hints.
1. Use of Valid Accounts / Compromised Credentials
- MITRE: T1550 / T1078 (Valid Accounts)
- Detect: anomalous logins (new geos), unusual admin console activity, unusually long sessions.
- Mitigate: force password resets for high-privilege accounts, enforce MFA, apply conditional access.
2. OAuth / Token Abuse (Cloud Account Compromise)
- MITRE: T1550.003 (Cloud Accounts) / Credential Access T1110
- Detect: new OAuth app grants, abnormal token issuance/refresh rates, suspicious API calls.
- Mitigate: rotate/revoke OAuth tokens, tighten app consent, apply least privilege to service principals.
3. Persistence and Long-Term Access
- MITRE: T1547 (Boot or Logon Autostart Execution), T1078 (Valid Accounts)
- Detect: long-lived sessions, new scheduled tasks, unusual service accounts.
- Mitigate: remove stale accounts, rotate secrets, audit long-term tokens/agents.
4. Bulk Data Exfiltration / Large-Scale Exports
- MITRE: T1041 / T1567 / T1074 (Data Staged)
- Detect: spikes in outbound traffic, large S3/DB GETs or export jobs, abnormal archive creation.
- Mitigate: egress controls, DLP on exports, alert on large data movement.
5. Command-and-Control / Signaling via Messaging Platforms
- MITRE: T1102 (Web Service) / T1071 (Application Layer Protocol)
- Detect: unusual webhooks or outbound connections to messaging APIs (Telegram, etc.).
- Mitigate: monitor and restrict outbound connections to non-approved services.
6. Public Proofing & Extortion (Impact/Influence)
- MITRE mapping: behavior linked to Exfiltration & Impact behaviours (not a single ATT&CK technique)
- Detect/Mitigate: monitor dark-web channels for sample postings; prepare legal/PR responses and evidence preservation.
Immediate defensive actions (prioritized)
- Treat the claim seriously – validate quickly. Request sample artifacts (hashes, screenshots, sample records) from the posting and preserve any original posting (screenshot + metadata). Do not engage or pay.
- Hunt for exfiltration indicators: search cloud storage access logs, database export logs, S3 GET/LIST spikes, large API responses, and unusual snapshot/export jobs.
- Audit OAuth and service principals: list and revoke unrecognized tokens and third-party app consents; require admin consent for new OAuth apps.
- Enforce and verify MFA: confirm MFA enforcement for all admin and customer-facing privileged accounts; temporarily require MFA revalidation where practical.
- Rotate sensitive credentials & keys: service accounts, API keys, OAuth client secrets, and any long-lived tokens.
- Preserve evidence & involve legal/IR: capture actor posts, coordinate with legal/regulatory teams, and prepare external communications.
- Monitor actor indicators: add shinygroup@tuta.com and actor strings to dark-web monitoring and SOC watchlists.
How to validate the claim
- Sample records (redacted sample rows) and matching SHA256 hashes of files.
- Proof links (Tor/onion URLs, paste links, marketplace postings).
- File artifacts to detonate in a sandbox and extract behavioral IoCs.
- Cloud activity logs showing large exports, recent admin API token use, or unusual service principal activity.
Bottom line
The Scattered Lapsus$ Hunters message is a high-impact extortion claim that lacks immediate technical proof in the posted text. That does not reduce its urgency, claim-driven extortion can prompt phishing, opportunistic fraud, and reputational pressure even when unverified. Security teams should prioritize validation and hunts for exfiltration indicators, lock down identity and OAuth surfaces, rotate credentials, and coordinate legal/PR response planning while preserving all evidence for potential investigations.
Disclaimer:
The information provided in this article is based on publicly available open-source intelligence (OSINT). It is intended for awareness and defensive cybersecurity purposes only.