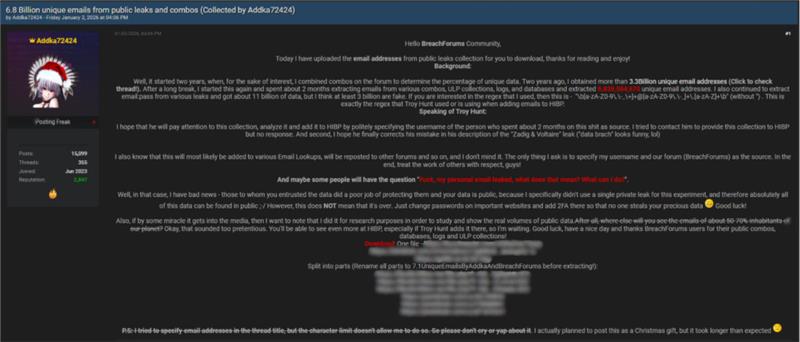
Threat actor Addka72424 claims ownership of a dataset containing 6.8 billion unique email addresses. The actor states the data was compiled from public leaks, historical breach data, stealer logs, ULP collections, and combolists. The dataset is framed as a large-scale aggregation effort rather than a single breach
Data sources
According to the threat actor, the dataset pulls from multiple previously exposed sources. These include from forums, telegram combolists, publicly circulated breach collections, stealer malware logs, and leaked databases. No claim of direct compromise or intrusion was made. The threat actor repeatedly emphasizes the public nature of the underlying data.
Collection timeline
The threat actor stated the compilation effort started two (2) years ago. Initial work focused on combining all email addresses from various sources to measure uniqueness across datasets. This phase allegedly resulted in more than 3.3 billion unique email addresses.
The threat actor also states a later two-month phase involved extracting email addresses from additional sources, which increased the final count to exactly 6,839,584,670 unique email addresses.
Email and password data
Beyond email-only records, the threat actor claims extraction of email and password pairs from multiple leak sources. The total volume is stated as roughly 11 billion records. The threat actor also claims at least 3 billion of these entries are fake or invalid, based on internal checks.
Technical details
The threat actor shared the regex used to extract email addresses during data processing.
\b[a-zA-Z0-9\.\-_\+]+@[a-zA-Z0-9\.\-_]+\.[a-zA-Z]+\b
The threat actor claims this pattern matches the one used by Troy Hunt when processing email addresses for Have I Been Pwned.
Reference to have I been pwned
The post directly references Troy Hunt and requests analysis of the collection for potential inclusion in Have I Been Pwned, with attribution to the threat actor. The threat actor claims previous attempts to contact Hunt and received no response. The post also criticizes an alleged error related to the description of the Zadig and Voltaire breach on HIBP.
Distribution expectations
The threat actor anticipates the dataset will surface across email lookup services and be reposted on multiple forums. The primary concern expressed involves credit attribution if redistribution occurs. The actor actively seeks engagement and visibility around the dataset.
Stated motivation
The threat actor frames the activity as research. The stated goal focuses on demonstrating the scale of publicly exposed email data and highlighting the volume of recycled breach material circulating across underground communities.
The information provided in this article is based on publicly available open-source intelligence (OSINT). It is intended for awareness and defensive cybersecurity purposes only.
AI used for formatting and grammar