Overview
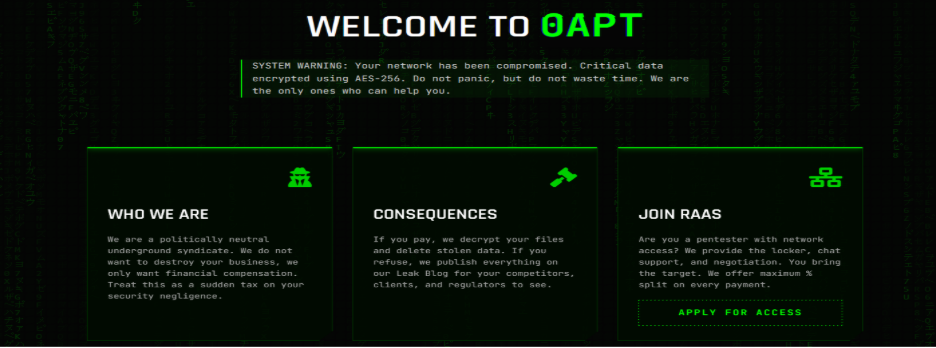
A newly identified ransomware group calling itself 0APT has emerged, operating a classic double-extortion model that combines data theft with encryption. Based on analysis of the group’s public data leak site and its “Active Operations” dashboard, 0APT appears to be actively targeting organizations across multiple sectors using a structured, time-driven extortion process.
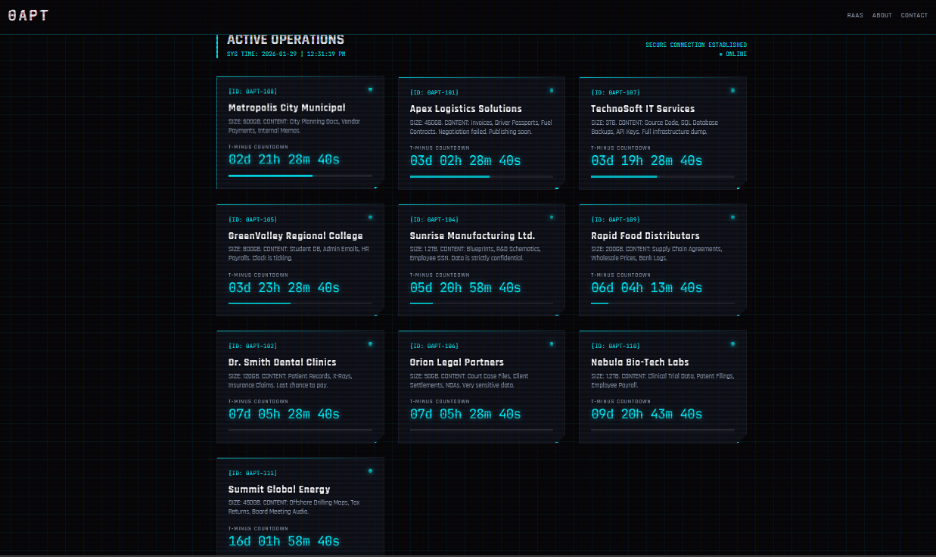
At the time of writing, the group lists eleven alleged victims, each accompanied by a visible countdown timer indicating when stolen data will be published if ransom demands are not met.
Key Observations
At a high level, 0APT can be summarized as follows:
- Threat Type: Ransomware / Double Extortion
- Threat Class: Cybercrime
- Operational Status: Active
- First Observed: January 28, 2026
- Leak Site Status: Online and actively updated
- Verification Status: Pending independent confirmation
Encryption Claims and AES-256
0APT claims to encrypt victim environments using AES-256, one of the strongest and most widely adopted encryption standards in use today. AES-256 (Advanced Encryption Standard with a 256-bit key) is a symmetric encryption algorithm that renders data unreadable without the correct decryption key.
While such claims are common among ransomware groups and should not be taken as unique on their own, the use of AES-256 aligns with industry-standard ransomware tooling and reinforces the likelihood that victims are facing real, recoverable only by key encryption events.
Alleged Victims
According to 0APT’s “Active Operations” panel, the following organizations are currently listed as victims:
- Metropolis City Municipal
- Apex Logistics Solutions
- TechnoSoft IT Services
- GreenValley Regional College
- Sunrise Manufacturing Ltd.
- Rapid Food Distributors
- Dr. Smith Dental Clinics
- Orion Legal Partners
- Nebula Bio-Tech Labs
- Summit Global Energy
- Quantum Financial Corp
Each listing includes a countdown timer, reinforcing urgency and signaling a well-defined extortion workflow rather than ad-hoc pressure tactics.
Target Profile and Victimology
Although the victim list is still small, early patterns are already visible.
Sector Targeting
0APT appears to follow a cross-sector, financially motivated targeting model, with a preference for data-rich and operationally sensitive environments:
- Government / Municipal: Public accountability, political pressure, and limited downtime tolerance
- Education: High concentrations of PII and historically weaker security budgets
- Legal Services: Confidential client data and reputational risk
- Manufacturing & Logistics: Supply-chain disruption leverage
- Energy & Biotech: Intellectual property value and regulatory scrutiny
This broad targeting supports the group’s claim of being “politically neutral,” with victim selection driven by leverage and payout potential, not ideology.
How 0APT Operates
0APT describes itself as a “politically neutral underground syndicate,” framing its activity as purely transactional. Behind the branding, however, the group appears to be running a Ransomware-as-a-Service (RaaS) operation.
The group openly advertises support for affiliates, offering:
- Encryption tooling
- Negotiation and chat support
- Leak site infrastructure
- Revenue sharing per successful payment
This structure allows 0APT to scale quickly by relying on affiliates for initial access while centralizing branding, negotiations, and data publication.
MITRE ATT&CK Mapping
At this stage, no malware samples or forensic artifacts have been publicly confirmed. As a result, ATT&CK mapping is inferred based on common double-extortion ransomware tradecraft rather than direct observation.
Likely tactics include:
- Use of valid credentials or exposed services for initial access
- Internal reconnaissance and privilege escalation
- Data collection and exfiltration prior to encryption
- Encryption of systems and inhibition of recovery mechanisms
This aligns closely with established ransomware operators rather than low effort or opportunistic actors.
Indicators of Compromise (IOCs)
As of now, no verified technical IOCs such as file hashes, command-and-control domains, or IP addresses have been publicly identified.
Currently Available Indicators (OSINT-Level)
- Leak site branding referencing “0APT”
- Consistent victim portal language and messaging
- Countdown based extortion UX
- Claims of AES-256 encryption
Defensive Considerations
Organizations should take the emergence of 0APT seriously and consider the following defensive steps:
- Monitor dark web and leak monitoring feeds for references to 0APT
- Harden internet-facing services and remote access infrastructure
- Validate backup integrity and offline recovery options
- Enforce least privilege access and credential hygiene
- Prepare incident response, legal, and notification playbooks in advance
Given the group’s emphasis on data theft, prevention and detection before encryption are critical.
Conclusion
0APT represents a new wave of ransomware operators that prioritize presentation, process, and psychological leverage as much as technical execution. Rather than operating opportunistically, the group appears structured, confident, and designed to scale.
The combination of data theft, encryption, countdown-driven pressure, and a RaaS model positions 0APT as a credible emerging threat across multiple industries. As more technical details surface, defenders should expect clearer insight into tooling and infrastructure, but early preparation remains the most effective defense.
Disclaimer: The information provided in this article is based on publicly available open-source intelligence (OSINT). It is intended for awareness and defensive cybersecurity purposes only.
