Introduction
The Lenotech Corporation, a Philippine-based technology, has been allegedly listed on a dark web onion site operated by the Tengu Ransomware Group, a newly observed ransomware-as-a-service (RaaS) threat group that was first observed in late October 2025. The threat group claims to have exfiltrated approximately 136 GB of internal data following an alleged security incident that has not been publicly acknowledged by the Lenotech company as of this moment..
Lenotech operates in the Philippines technology sector, offering products and services that include computer peripherals and accessories, laptops and storage devices, gaming accessories, and dash cameras. The company distributes products from brands such as A4Tech, Lenovo, and Seagate, serving both individual consumers and business clients, and also provides marketing support and dealer application services. Lenotech was confirmed to be listed as an Authorized Service Center for Lenovo, responsible for warranty repairs, diagnostics, and device servicing. At this time, there is no evidence indicating that Lenovo’s corporate network or systems were compromised.
All the details in this report are derived solely from the threat group’s disclosures and remain unverified.
Threat Group Profile: Tengu Ransomware Group
Tengu is an emerging ransomware operation that surfaced in the threat landscape in October 2025. Public reporting on the group remains limited, but observed activity suggests alignment with organized cybercriminal operations offering ransomware-as-a-service capabilities.
Observed Characteristics
- Operation of a dedicated Tor-based data leak site
- Use of double extortion tactics, prioritizing data theft and public exposure
- Publication of selective data samples to support extortion claims
- Employment of countdown timers to pressure victims during negotiation windows
While Tengu’s tooling, affiliates, and infrastructure are not yet well documented, its operational model mirrors that of established ransomware groups, suggesting a deliberate attempt to rapidly build credibility within the ransomware ecosystem.
Alleged Disclosure via Onion Site
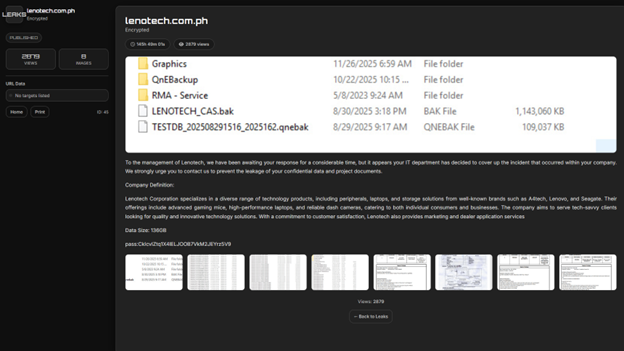
The alleged incident was disclosed through a Tor-based onion site platform associated with Tengu. In the post, the group accused Lenotech of failing to respond to outreach attempts regarding the incident. As of publication, Lenotech has not issued a public statement confirming or denying the claims, and all available information remains unverified and sourced solely from the threat actor.
Allegedly Exfiltration Data
According to the samples, the threat group claims to have gained access to Lenotech’s internal systems and backups. Visible directory listings and file previews suggest the allegedly exfiltrated data may include operational and service-related information.
The folders and files displayed by the actor include:
- Internal directories labeled Graphics, QnEBackup, and RMA Service.
- Backup and archive files.
- File timestamps ranging from August 2025 through November 2025.
Preview images uploaded by the group appear to show databases, service logs, internal documentation, and system-generated records. However, the full dataset has not been released publicly, and the authenticity, scope, and sensitivity of the alleged data cannot be independently verified.
Claimed by the Threat Group
- Exfiltration of ~136 GB of internal Lenotech data
- Access to internal systems and backups
- Non-responsiveness from Lenotech during outreach attempts
At this stage, the incident remains unconfirmed, and no independent evidence has been made public to validate the threat group’s claims. Nevertheless, the presence of structured directory listings, file previews, and a timed release mechanism indicates a credible data extortion attempt consistent with contemporary ransomware operations.
Tactics, Techniques, and Procedures (TTPs)
The following TTPs are based on actor claims and observed leak site behavior and should not be considered confirmed intrusion details.
Initial Access (Alleged)
- Possible exploitation of exposed services or stolen credentials (unconfirmed)
Credential Access & Persistence (Alleged)
- Access to internal backups and service-related systems
- Potential use of valid accounts (claimed, not verified)
Data Collection & Exfiltration
- Aggregation of internal files and backups
- Exfiltration of data prior to public disclosure
Extortion
- Threat of public data release
- Countdown-based pressure tactics via onion site
MITRE ATT&CK Mapping (Indicative)
The table below maps alleged and observed behaviors associated with this incident to the MITRE ATT&CK framework. These mappings are defensive and analytical in nature and do not confirm exploitation.
| ATT&CK Tactic | Technique ID | Technique Name | Relevance to Case | Evidence Level |
|---|---|---|---|---|
| Initial Access | T1078 | Valid Accounts | The threat group claims access to internal systems, which may imply misuse of legitimate credentials. | Claimed by the threat group. |
| Credential Access | T1552 | Unsecured Credentials | Access to backups may indicate exposure of stored credentials. | Inferred and unverified. |
| Persistence | T1078 | Valid Accounts | Continued access implied by multi-month file timestamps. | Claimed by the threat group. |
| Collection | T1005 | Data from Local System | Internal files and service-related data allegedly collected. | Sample screenshots. |
| Collection | T1039 | Data from Network Shared Drive | Presence of backup and archive directories. | Inferred |
| Exfiltration | T1567 | Exfiltration over Web Services | Common method in data-centric extortion campaigns. | Suspected |
| Exfiltration | T1041 | Exfiltration over C2 Channel | Possible alternative exfiltration path. | Theoretical |
| Impact | T1565 | Data Manipulation | Risk of data exposure or misuse | Potential impact |
| Impact | T1486 | Data Encrypted for Impact | Not observed; extortion appears data-centric. | Not observed |
Indicators of Compromise (IOCs)
At this time, no verified technical indicators (hashes, IP addresses, domains) have been publicly released that can be reliably associated with this alleged incident. Organizations should treat any purported IOCs related to this case with caution unless corroborated by trusted sources.
Conclusion
The alleged compromise of Lenotech Corporation underscores the ongoing shift in ransomware activity toward data-centric extortion, where the threat of public exposure is used as primary leverage rather than system disruption alone. Although the claims made by the Tengu Ransomware Group remain unverified, the structure of the onion site, the publication of selective data previews, and the use of a timed release mechanism are consistent with established ransomware extortion practices.
This situation remains active and evolving. Additional developments may emerge should Lenotech issue a public statement, negotiations reach a resolution, or the threat group proceed with releasing the purported data. Stakeholders and organizations within the region are advised to monitor the situation closely and treat it as a relevant example of contemporary ransomware and data extortion risks.
