The Morocco data breach has become the country’s most severe cybersecurity incident to date, compromising personal information linked to nearly 2 million employees and affecting over 500,000 businesses.
This major attack, allegedly carried out by the Algerian hacker group Jabaroot DZ, targeted the National Social Security Fund (CNSS) and the Ministry of Economic Inclusion, Small Business, Employment and Skills (MIEPEEC).
According to experts, the hackers exploited a zero-day vulnerability within a third-party Oracle-based system to bypass internal defences. The attackers managed to exfiltrate large volumes of unencrypted data, later leaking the files on Telegram, which is a sign that the motive may be political rather than financial, as no ransom was demanded.
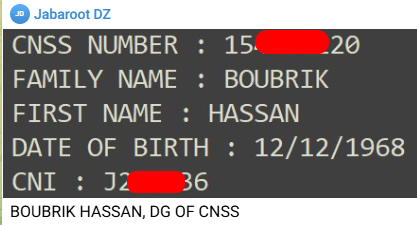
Among the stolen data were sensitive documents such as salary certificates, employee databases, and records tied to key organisations, including Morocco’s royal holding company SIGER and the Israeli liaison office in Rabat. Jabaroot DZ even leaked the personal details of CNSS Director General Hassan Boubrik, challenging the agency’s public denial of the breach.
This Morocco data breach has reignited concerns about the country’s ongoing cybersecurity deficiencies.
Despite warnings following a 2020 breach that exposed data from 3.5 million users, institutions have failed to address weak access controls, insufficient encryption, and poor third-party oversight. Analysts now call for the urgent adoption of decentralised security architectures, zero-trust models, and real-time threat detection to avoid future compromises.

In response to the attack, Moroccan hacker group Phantom Atlas retaliated by seizing more than 13GB of confidential data from the internal systems of Algeria’s General Post and Telecommunications Corporation (MGPTT) just 24 hours after the CNSS attack, including personal records and critical strategic documents, with some accounts indicating the breach could be as large as 20GB.
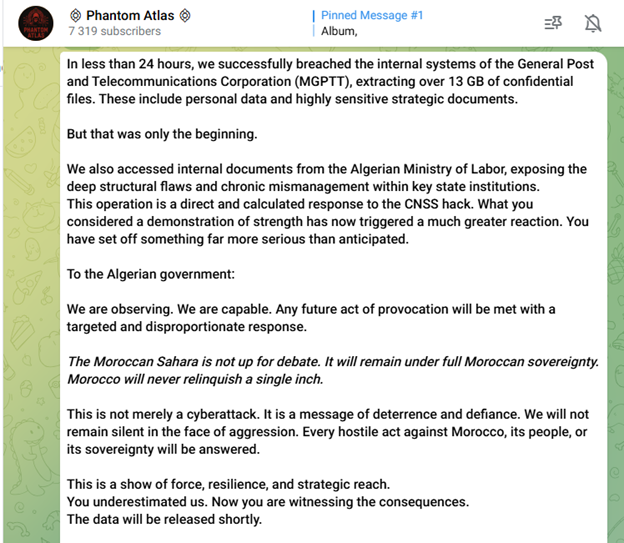
Another Moroccan group, OPx005, followed up with DDoS attacks on various Algerian ministries, including Defence and Foreign Affairs. Phantom Atlas warned Algerian officials that “every hostile act against Morocco will be answered,” referencing the Western Sahara conflict as part of their message.
The Morocco data breach is seen as part of a growing cyber conflict between Moroccan and Algerian hacking communities. What started with symbolic website defacements has evolved into high-impact cyberattacks, with the potential to threaten critical national infrastructure such as telecommunications, transport networks, and energy systems.
International experts are urging Moroccan authorities to take immediate steps to monitor leaked data, conduct full security audits, improve staff cyber awareness, and seek global cybersecurity cooperation. Analysts also recommend initiating regional cyber diplomacy to prevent an ongoing cycle of retaliation.
Other recent attacks in the region include claims by Tunisian group RootStorm, which compromised Moroccan platforms like Mt Cash and SIG Maroc, targeting infrastructure-related systems and reinforcing the urgent need to modernise cybersecurity defences.
The Morocco data breach stresses how cybersecurity is no longer a technical concern alone but is now deeply intertwined with regional politics, national security, and public trust.
Recommendation for the companies in the targeted countries/regions:
Immediate Actions:
- Alert local ISP / Hosting Provider: Request filtering or rerouting.
- Enable DDoS Protection: Use services like Cloudflare, Akamai, AWS Shield, etc.
- Geo-blocking & Rate Limiting: Block non-essential regions and limit request rates.
- Activate CDN & WAF: Offload traffic and block malicious requests.
- Monitor Traffic: Watch for spikes or anomalies using network monitoring tools.
Response & Coordination:
- Notify CERT / CSIRT: Report incidents for national-level support.
- Engage Law Enforcement: Especially if the attack is targeted.
- Communicate Clearly: Inform customers and stakeholders.
At iZOOlogic, we specialise in proactive threat intelligence and risk mitigation through our Dark Web Monitoring and Attack Surface Monitoring services.
If your organisation is in a region currently being targeted by DDoS attacks or other cyber threats, our solutions can help you:
- Identify Early Warnings: We monitor underground forums, threat actor channels, and marketplaces to detect potential attacks before they happen.
- Expose Vulnerabilities: Our attack surface monitoring detects exposed assets and misconfigurations that attackers may exploit.
- Track Threat Actor Activity: We provide real-time insights into chatter and campaigns targeting your industry or region.
- Reduce Response Time: With early intelligence and asset visibility, your team can act faster and smarter.
Whether you’re under attack or preparing for one, iZOOlogic is your partner in staying one step ahead.
Contact us to learn how we can strengthen your digital defences.
