Observed activity:
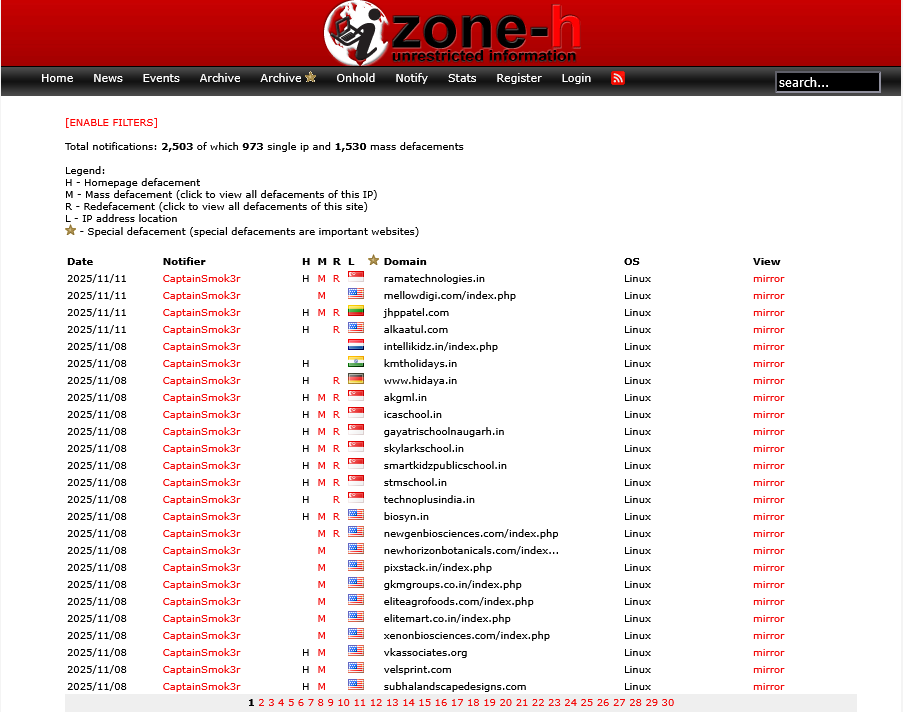
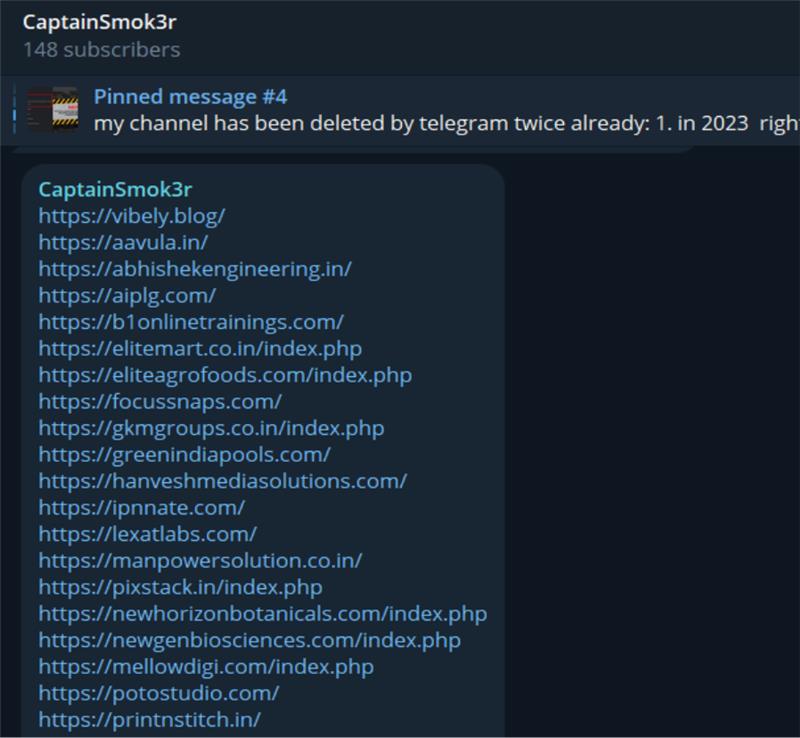
A cybercriminal group calling itself CaptainSmok3r has been observed compromising 150+ Indian websites, causing operational disruption, data exfiltration, and establishing persistent remote access. Recent public records and mirrors show multiple defacements and archived notifications attributed to this notifier.

Technical / Behavioural analysis:
- Compromised sites exhibiting weak passwords, no MFA, and missing EDR/antivirus.
- The actor publicly advertises and sells access (webshells, cPanel access, SMTP/mailers and similar illicit services) via channels where they post samples and sale offers. Administrators/handles tied to the activity include @imsmok3r and @altafhossainff.
Observed impacts:
- Business downtime / operational disruption.
- Data theft and likely resale of credentials/access.
- Persistent remote footholds enabling follow-up intrusions.
Indicators / sources to follow:
- Zone-H defacement archive entries under notifier CaptainSmok3r (mirrors and records exist).