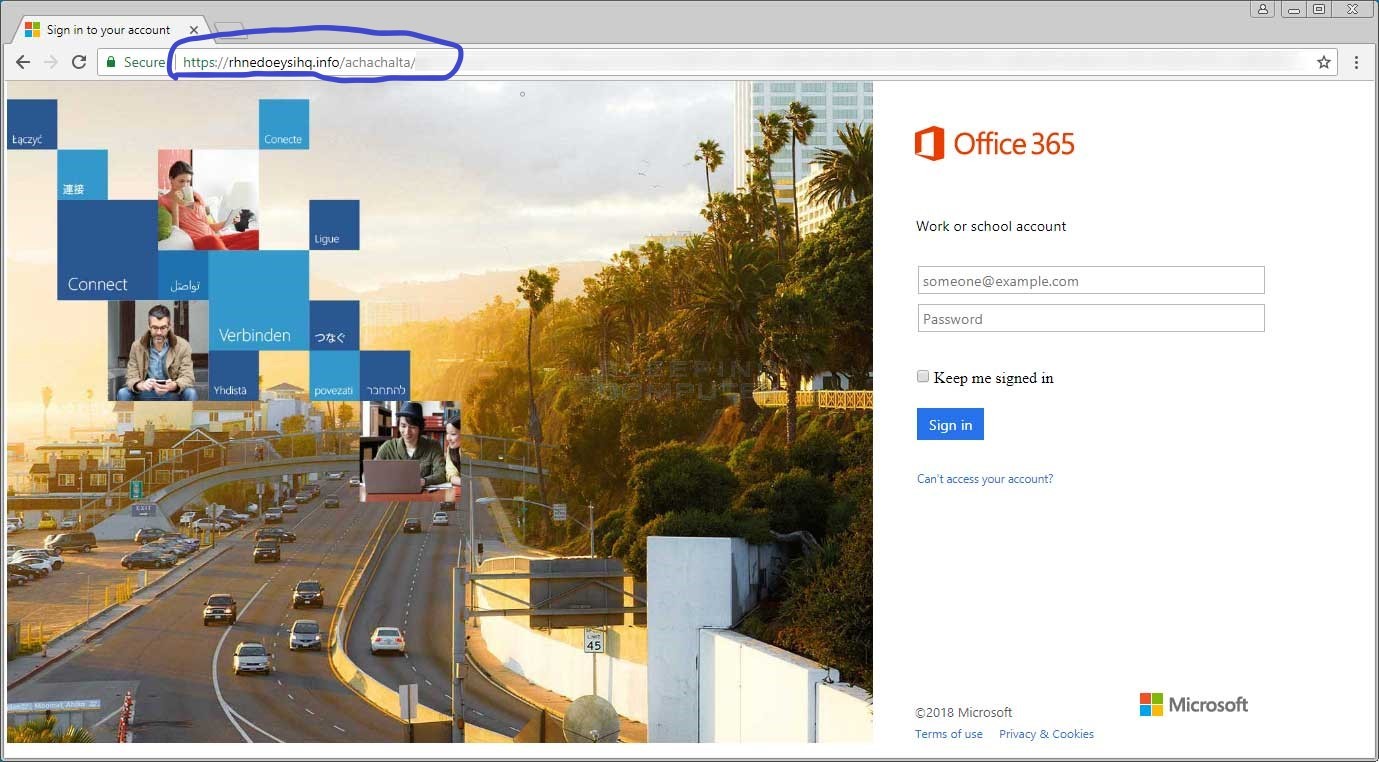
Baiting Scheme Legitimately looking organization newsletter subscription forms to scam…
Solutions
Attack Surface Management
Cyber Threat Intelligence
Brand Intelligence
Threat Management
Third Party Risk Management
Attack Surface Management
Cyber Threat Intelligence
Brand Intelligence
Threat Management
Third Party Risk Management