The Rise of a Controversial Threat Actor
In the world of underground dark forums and cybercrime networks, a threat actor who has declared themselves as Machine1337, which is also using the alias EnergyWeaponUser, has gained widespread global attention. His first appearance emerged on the Russian-language forum named “XSS” in January 2024, portraying himself as a red-team expert. He quickly established credibility in XSS by posting exploit development and API abuse, particularly methods for bypassing mobile authentication. His English fluency, technical depth, and frequent engagement have stood out in the crowd. After his reputation grew, he shifted his attention to using aggressive tools that target SMS and APIs – a strategy that caught attention across DarkForums and Telegram. With his regular technical contributions were emphasized by the forum users, and by May 2025, he was being actively discussed in Telegram breach-trading circles. He shifted again in his activities and, combined with his well-marketed data breach allegations, transitioned from being an underground educator to presenting himself as a high-profile data broker.
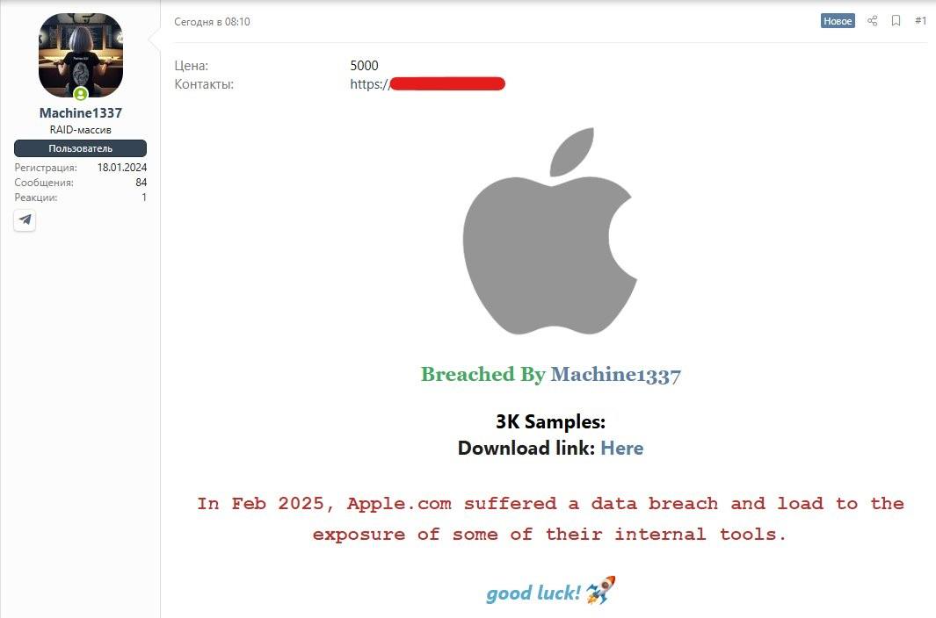
Early this year, the threat actor had taken a bolder move—becoming a self-proclaimed data broker. His breach claims are linked to well-known companies like Apple, Steam, Coinbase, Snapchat, Temu, and many more, attracting greater attention and concern from the cybersecurity community. As a result, his name quickly became more well known.
Behind his polished posts, eye-catching sample files, and well-crafted marketing, signs are growing that Machine1337 may be running a much larger fraud operation. There is evidence collected from underground forums, leak sites, and dark web marketplaces that suggests that this threat actor isn’t just selling data—he may be just actively fabricating, manipulating, or recycling it to mislead buyers and boost their reputation.
Profiling Machine1337
- Aliases: Machine1337, EnergyWeaponUser
- Language: English
- Operational Reach: BreachForums, DarkForums, XSS, and Telegram channels.
- Motivation: Reputation building and monetization through alleged breach claims.
- Modus Operandi: The use of recycled or fabricated SMS-style data to mimic real breaches and selling it with a limited-time download links.
- Skill Level: Moderate technical ability—a good skill in marketing and repacking data.
- Risk Level: Medium—he creates a reputational threat, although the genuine breach evidence remains unverified.
- Suspected Connections: IntelBroker and Zjj (based on shared behaviors, similar language use, overlap in forum activity on XSS and DarkForums, and concurrent breach timing patterns)
The Machine1337 doesn’t operate the same way as other hackers. His posts often come with high-quality banners, clear encryption guides, and detailed FAQs—giving the impression of a professional, trustworthy operation. This polished style helps build credibility and attract buyers, but it may also be part of a strategy for fraudulent activity.
Analyzing the Timeline of the Alleged Claims Pattern
The iZOOlogic Threat Intelligence team has conducted a comprehensive analyzation through posts, breach claims, and forum behaviors linked to the threat actor “Machine1337”. These were observed across XXS, DarkForums, BreachForums, and Telegram. The following observations summarize Machine1337’s attack pattern from early 2024 to mid-2025.
-
Cross-Platform Duplication and Sock puppetry:
In April 2025, Machine1337 posted a dataset for sale on Telegram, claiming that it contained 10.9 million records from an Indian bank. Around the same time, an identical post appeared on BreachForums under the alias “M0rSec”—featuring the same dataset description, formatting, and language.
Although there is no concrete evidence that Machine1337 and M0rSec are the same person, the timing, structure, and content of the posts are nearly identical. This strongly suggests the possibility of sock puppet behavior which is a common tactic where a threat actor uses multiple aliases to create the illusion of credibility, engagement, or third-party confirmation.
In reputation-driven cybercrime markets, where criminals use multiple identities to repost their own leaks or vouch for themselves in an effort to appear more active, supported, or “trusted,” this type of cross-posting behavior is very common. This is a well-known tactic used to artificially boost credibility, manipulate forum dynamics, and deceive potential buyers. By creating the illusion of community validation or third-party endorsements, threat actors can boost the visibility of their posts and increase the chances of monetizing fraudulent or recycled data.
-
Lack of Source Verification:
None of the posts reviewed showed clear proof of where the breaches came from. While sample files were often shared through sharing platforms and were sometimes packaged with banner images and FAQ-style write-ups, there was no real evidence to support the breach claims, such as access logs, exploit details, or insider confirmation.
-
Fraud-Centric Operational Model:
The threat actor’s whole breach operation appears to be built on his reputation farming rather than advanced intrusion. With a focus on visual presentation, dramatic titles, and recycled data samples, Machine1337’s campaign shows characteristics of a low-technical but high-social engineering threat actor, aiming to grow influence and possibly earn from fabricated leaks.
What the Data Actually Shows
iZOOlogic and other researchers analyzed multiple datasets shared by Machine1337 across forums and Telegram. The analyzed data shows consistent signs of data manipulation, recycled content, and poor authenticity. The key observations are:
-
Identical Data Structures Across Different Breach Claims
Leaks attributed to Apple, Steam, and Huawei all used the same table format and fields, despite allegedly coming from entirely different infrastructures. This strongly suggests template reuse or data fabrication.
-
Rapid Expiration of Hosting Links
Links to download sample data were often deleted or expired within hours, limiting any meaningful third-party validation. This behavior suggests an effort to evade verification while maintaining an appearance.
-
No Official Breach Confirmations from Alleged Victims
As of July 2025, there are no disclosures, press releases, or breach confirmations from companies named by Machine1337, including Apple, Steam, Binance, and Shopee.
-
What Does the Public in the Forums Really Think About Machine1337?
In the platforms like Reddit, Telegram, and BreachForums clones, users have increasingly questioned the legitimacy of Machine1337, often comparing him to other cyber fraudsters who relied on “fear marketing” tactics creating panic and urgency around exaggerated breach claims to drive attention or quick sales.
Why is this a Global Concern?
Even when breach claims turn out to be false or exaggerated, the real-world consequences can still be serious. Fake leaks can cause reputational harm, mislead security teams, and be weaponized for fraud and social engineering. Here’s why Machine1337’s tactics and others like them should not be ignored.
-
Phishing & Social Engineering Risks
Even if the data is outdated or fabricated, real phone numbers or names in these dumps can be used to launch targeted phishing campaigns, impersonation attempts, or spam attacks.
-
Reputational Damage to Brands
Companies falsely associated with leaks face public backlash, loss of customer trust, and potential regulatory scrutiny, even if the data is proven to be fake.
-
Scam Monetization via Fear
Threat actors use fear-based marketing tactics to lure buyers into paying for fake or recycled datasets, contributing to the underground economy of digital fraud.
Strategic Recommendations
To help organizations navigate these risks, iZOOlogic recommends the following proactive measures for businesses, governments, and private infrastructure providers:
-
Thoroughly Validate Breach Claims
Before issuing public statements or launching incident responses, confirm the legitimacy of leaked datasets through internal cross-referencing and forensic checks.
-
Cross-Check Exposed Data
Investigate whether data fields (examples phone numbers, timestamps, message IDs) match any known system outputs or third-party integrations.
-
Continuously Monitor Underground Channels
Track dark web forums and telegram groups for repeat patterns, aliases, or suspicious marketing tactics linked to false breach activity.
-
Report Known Fraud Threat Actors
Share indicators of fake breach behavior with industry partners, CERTs, and intelligence networks to reduce amplification and prevent buyer exploitation.
Conclusion
The case of Machine1337 shows a growing threat in the cyber underground, the threat actors who care more about attention than truth. They use recycled test data, fear-based tactics, and polished presentations to look more credible and make money. Even though his breach claims lack solid technical proof, the risks are still real, like phishing attacks using leaked phone numbers or damage to the reputation of companies wrongly linked to these fake breaches.
Our investigation, supported by data validation, community sentiment, and analysis of forum behavior, strongly suggests that Machine1337’s operations are fraud-centric, rather than breach-driven. The consistent use of cross-platform aliasing and rapid link deletion all point to an actor more focused on attention and manipulation than technical exploitation.
For organizations, this case highlights the importance of validating breach claims, monitoring underground chatter, and educating stakeholders on the increasing sophistication of cybercriminal social engineering. As the boundary between real and fake data blurs, so too must our vigilance.
Disclaimer:
The information provided in this article is based on publicly available open-source intelligence (OSINT). It is intended for awareness and defensive cybersecurity purposes only.