A newly emerged cybercriminal group, Coinbase Cartel, has entered the threat landscape with a distinct approach to ransomware operations. Unlike traditional gangs that rely on encryption, Coinbase Cartel focuses solely on data exfiltration. Their operations are business-like, leveraging staged data leaks, professional negotiations, and partnerships to maximize extortion success.
Initial Discovery
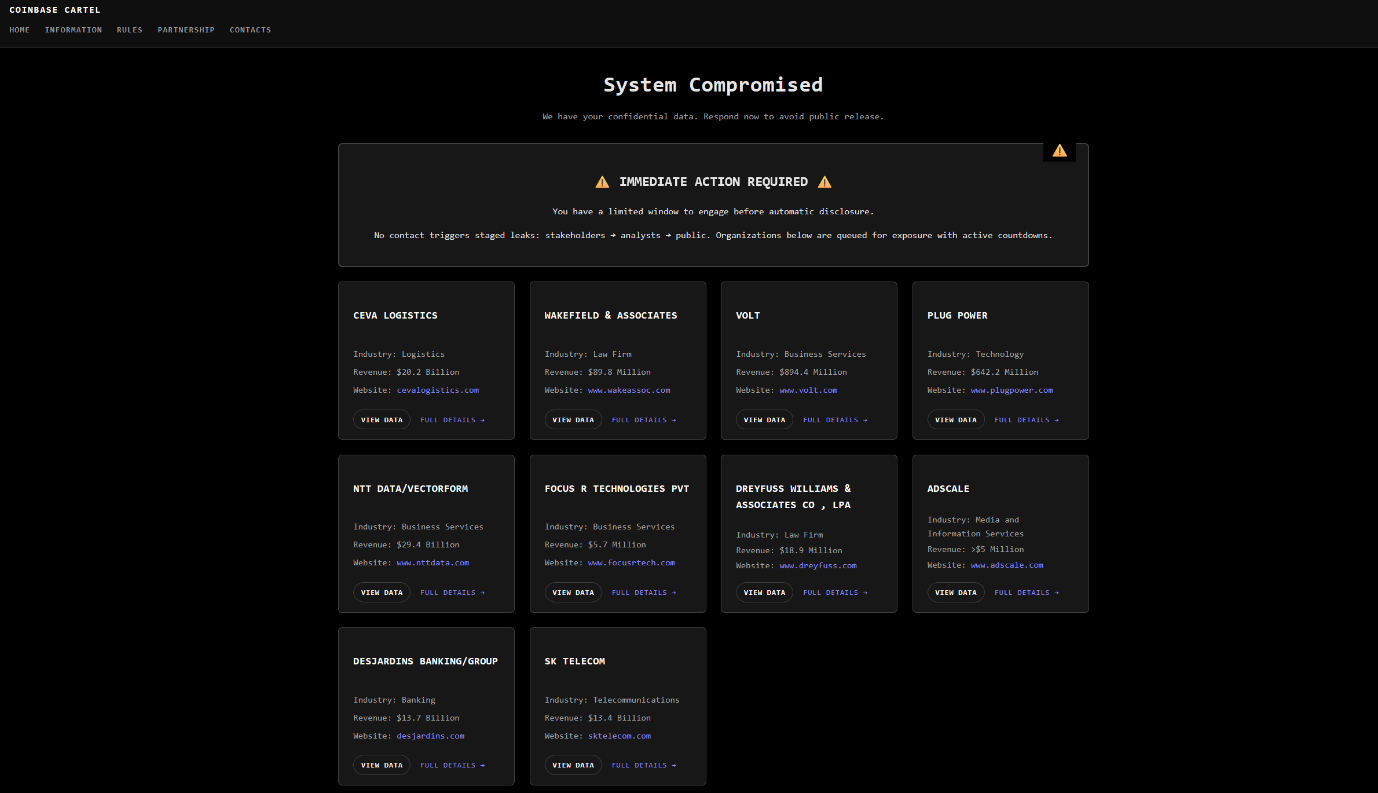
Coinbase Cartel was identified after a series of data leak incidents across multiple industries. Investigations revealed that the group does not deploy encryption or disrupt business operations; instead, they extract sensitive data and use it as leverage during negotiations.
Threat Actor Profile
Group Name: Coinbase Cartel
Motivation: Financial – pure extortion through stolen data
Target Sectors: Logistics, Law Firms, Technology, Business Services, Media & Information, Banking, Telecommunications
Geographic Focus: South Korea, Canada, Israel, United States, Japan, Europe
Victim Profile:
Coinbase Cartel has targeted organizations across logistics, banking, telecommunications, technology, law firms, and business services, with confirmed victims spanning South Korea, Canada, Israel, the United States, Japan, and Europe. Notable names include Desjardins Group, AdScale, CEVA Logistics, Wakefield & Associates, and NTT Data.
Attack Vectors
- Exposed or hardcoded credentials in source code
- Leaked repository access keys (e.g., AWS, Bitbucket, GitHub)
- Insider-assisted access verification
- Poor segmentation exposing internal tools and repositories
Tactics, Techniques & Procedures (TTPs):
- Credential access via valid accounts, cloud credentials, and repositories.
- Data collection and staging from internal systems.
- Staged leaks to apply pressure during extortion.
- Professional negotiations with proof-of-data packages.
- Partnership outreach offering fixed-rate or revenue-sharing deals.
Impact
Victims face sensitive data exposure, reputational damage, and amplified media involvement. The absence of encryption allows operations to continue, but reputational and legal risks escalate as staged leaks progress.
Mitigation & Recommendations
- Enforce strict credential rotation and access management.
- Secure cloud environments and repositories against exposed keys.
- Monitor for unusual outbound data transfers and staged file archives.
- Deploy insider threat monitoring and segmentation controls.
- Conduct regular threat hunting aligned with MITRE ATT&CK techniques.
behavior, such as compressed archives or structured exports of databases (e.g., backupset, restorehistory, ClientCheckUSD)
Conclusion
Coinbase Cartel represents a shift in ransomware strategy, abandoning encryption in favor of stealthy, data-only extortion. Their calculated, partnership-driven approach demonstrates the objective of cybercrime, where reputation, insider collaboration, and controlled leaks are leveraged to maximize financial gain.
The group’s emergence highlights the need for organizations to strengthen credential security, cloud defense, and insider monitoring to stay ahead of evolving data-extortion models.
How iZOOlogic can help:
At iZOOlogic, we specialize in detecting, monitoring, and mitigating advanced cyber threats such as those posed by emerging groups like Coinbase Cartel. Our solutions are designed to help organizations stay ahead of evolving extortion tactics.
Disclaimer: The information provided in this article is based on publicly available open-source intelligence (OSINT). It is intended for awareness and defensive cybersecurity purposes only.
