A new, highly advanced Phishing-as-a-Service (PhaaS) operation named Darcula has emerged from the dark corners of the cybercrime world — and it’s making waves. Security researchers recently uncovered that this operation has stolen over 884,000 credit cards, targeting users globally via deceptive text messages that impersonate legitimate services.

Darcula isn’t your average phishing scam. It’s a full-fledged phishing ecosystem, offering cybercriminals a plug-and-play platform to launch convincing smishing attacks — and it’s already active in over 100 countries.
The threat actors behind the Darcula PhaaS platform appear to be readying a new version that allows prospective customers and cyber crooks to clone any brand’s legitimate website and create a phishing version, further bringing down the technical expertise required to pull off phishing attacks at scale.
What Makes Darcula So Dangerous?

Darcula redefines smishing by:
- Using iMessage and RCS instead of SMS – bypassing traditional spam filters
- Spoofing major brands and government agencies with pixel-perfect websites
- Hosting over 20,000 and more phishing domains that rotate rapidly to avoid detection
- Offering a full suite of phishing tools as a service, with multilingual support
Anatomy of the Attack

Here’s how a typical Darcula smishing campaign unfolds:
- Phishing Text Sent: You receive a message like “Royal Mail: Your parcel is on hold due to unpaid customs. Pay now: [malicious link]”
- Fake Website: Clicking the link opens a fake Royal Mail page asking for credit card details, DOB, and OTPs.
- Card Data Exfiltrated: Your information is instantly harvested and sent to Darcula’s backend, where it’s stored, sorted, and often sold on underground markets.
- No Red Flags: Because iMessage and RCS don’t rely on SMS gateways, your mobile security tools might not catch the threat quickly.
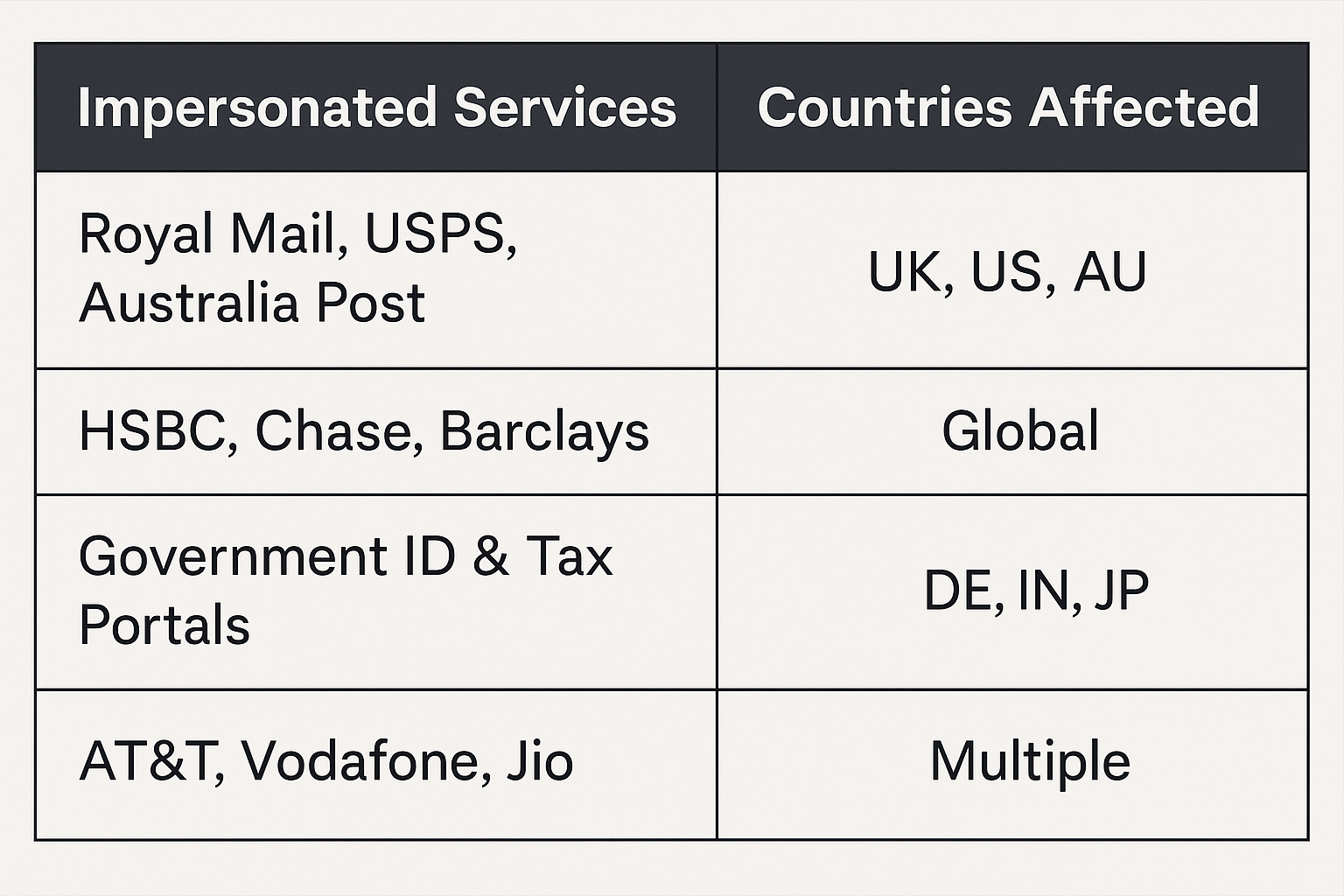
Who’s Being Targeted?
Darcula’s infrastructure includes fake portals impersonating:
Under the Hood: How Darcula Works
Darcula is not just a phishing page generator — it’s a comprehensive criminal platform with:
- A user dashboard for tracking stolen data
- Real-time notifications of successful phishing
- Tools to spoof 2FA pages, OTPs, and mobile apps
- Bulletproof hosting + fast-flux DNS to evade takedowns
It’s marketed and sold on Telegram channels and dark web forums, with subscription packages ranging from $100 to $1000/month based on the features.
Indicators of Compromise (IoCs):
A sample of Darcula-linked domains:
- secure-idgov[.]co
- track-parcels[.]online
- usps-alert[.]top
- auspost-track[.]net
Impact: The Financial Fallout
According to multiple threat intel sources:
- 884,000+ stolen card records (count traced and shared by a security researcher from NRK)
- Estimated fraud impact: $ 50 M+
- Dozens of companies impersonated
- Continuous evolution with fresh domain rotations daily
How to Stay Protected
For Individuals:
- Never click links in texts from unknown senders
- Enable SMS filtering or install security apps like Lookout, Bitdefender, or Microsoft Defender
- Check your statements for suspicious transactions
- Freeze your credit if in doubt
For Organisations:
- Monitor for phishing domains impersonating your brand
- Launch internal smishing awareness training
- Use brand protection tools to scan for malicious lookalikes
- Work with telecoms to block RCS/iMessage abuse
Darcula is an example of how cybercrime has become productised. With little effort, even low-skilled threat actors can now launch sophisticated phishing attacks that bypass traditional defences.
As we move further into 2025, smishing and PhaaS operations like Darcula will continue to grow in complexity.
At iZOOlogic, we specialise in detecting and mitigating brand abuse, phishing attacks, and online impersonation threats that can damage your reputation and defraud your customers. Our comprehensive threat intelligence platform monitors the surface, deep, and dark web to identify and take down phishing sites, fake domains, rogue mobile apps, and unauthorised use of your brand.
Stay one step ahead of cybercriminals—safeguard your brand, customers, and digital presence with iZOOlogic’s real-time brand protection and phishing detection services.
