Cookies are an integral part of web applications, often used to store session information or user preferences. When the domain attribute of a cookie is set too loosely, it increases the risk of unintended access by subdomains, which can lead to various security vulnerabilities, such as session hijacking or data leakage.
What is the Domain Attribute in Cookies?
The Domain attribute specifies the scope of a cookie, determining which domains and subdomains can access it. By default, a cookie is accessible only to the domain that set it. When the Domain attribute is explicitly set, it may allow subdomains to access the cookie.
Risk of a Too-Loose Domain Setting
- Unintended Subdomain Access: Cookies may be accessible to all subdomains, including those less secure or operated by third parties.
- Session Hijacking: A compromised subdomain can steal cookies shared across the domain.
- Cross-Site Scripting (XSS): Subdomains vulnerable to XSS can access cookies and escalate attacks.
- Increased Attack Surface: Expanding the cookie scope makes it harder to secure all potential access points.
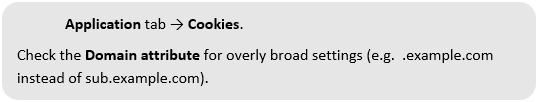
How to Identify a Loose Domain Attribute
Use browser developer tools (e.g., Chrome DevTools):
How to Fix Loose Domain Attribute
Best Practices for Setting the Domain Attribute:
- Restrict the Domain Scope: Set the Domain attribute to the specific subdomain where the cookie is required.
- Avoid Wildcards: Do not use overly broad domains (e.g., .example.com) unless absolutely necessary.
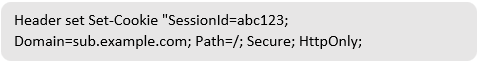
Web Server Configuration
- Apache: Add a restrictive domain in your .htaccess file or server configuration:
- IIS: Configure HTTP response headers to include the HttpOnly flag in cookies.
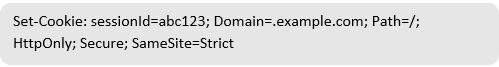
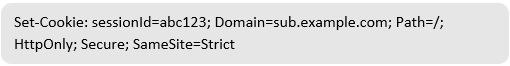
Example of a Secure Cookie
Before Fix:
After Fix:
Benefits of a Restricted Domain Attribute
- Limits Cookie Exposure: Restricting the domain ensures that only specific subdomains can access cookies.
- Reduces Attack Surface: Minimizes the risk of cookie theft from compromised subdomains.
- Improves Security Posture: Enhances control over cookie access and reduces unintended data leakage.
Limitations
- Complex Subdomain Management: Applications with numerous subdomains may require additional configuration to ensure proper cookie handling.
- Legacy Dependencies: Some older applications may rely on shared cookies across subdomains
Conclusion
Setting a cookie’s domain too loosely can expose it to unnecessary risks. By restricting the domain attribute to the specific subdomain where the cookie is needed, you can significantly enhance the security of your application, reduce the risk of session hijacking, and maintain tighter control over user data.
References
https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Set-Cookie