CRLF (Carriage Return Line Feed) injection is a web security vulnerability that occurs when an attacker injects unexpected CRLF characters into a web application. This vulnerability is typically exploited by manipulating HTTP headers or injecting malicious input into other areas of an application.
What Are CRLF Characters?
A Carriage Return Line Feed (CRLF) injection attack, also referred to as an HTTP response splitting attack, is a type of cyber threat that manipulates the carriage return and line feed special characters found within a web application’s HTTP header. This type of attack can lead to various adverse consequences, ranging from cross-site scripting and cookie injection to phishing attacks and web cache poisoning.
- Carriage Return (\r): Moves the cursor to the beginning of the line.
- Line Feed (\n): Moves the cursor down to the next line.
How Does CRLF Injection Work?
CRLF injection exploits improper input handling, allowing an attacker to insert \r\n characters. This injection can manipulate HTTP responses and headers, leading to:
- HTTP Header Injection:
- Attacker appends malicious headers.
- If unvalidated, the application includes the injected headers in its response.
- Attacker appends malicious headers.
- Web Cache Poisoning:
- Attackers manipulate cache behaviour by injecting headers like Cache-Control.
- Malicious pages are cached and served to other users.
- Cross-Site Scripting (XSS):
- Malicious input can create new lines that allow JavaScript injection.
- Log Injection:
- Injected CRLF can alter log file entries, leading to log manipulation or evasion.
Use Cases of CRLF Injection
- Phishing Attacks: Manipulate content on a trusted site to redirect users or display malicious content.
- Session Hijacking: Alter cookies or headers to take over user sessions.
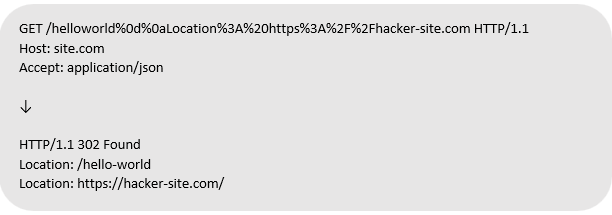
Exploitation
This request exploits HTTP response splitting by injecting CRLF characters (%0d%0a) into the URL. The server interprets the request as two separate headers, leading to multiple Location headers in the response. This can cause unpredictable behaviour, such as redirecting users to https://hacker-site.com/, enabling open redirect or cache poisoning attacks if improperly handled.
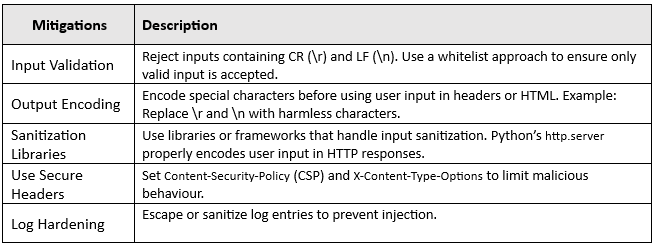
Mitigation and Fixes
Conclusion
CRLF injection is a significant threat when input handling is poorly implemented. By validating and sanitizing input, encoding outputs, and adopting secure development practices, developers can mitigate this vulnerability effectively.
Reference
https://owasp.org/www-community/vulnerabilities/CRLF_Injection