What is X-Content-Type-Options?
X-Content-Type-Options is an HTTP response header used to enhance the security of a web application. It prevents browsers from interpreting files as a different MIME type than what is specified by the server. This header is particularly useful in mitigating MIME-type sniffing attacks, where malicious actors exploit browser behaviour to execute unintended scripts or files.
Purpose and Use Cases
- Preventing MIME-Type Sniffing: By default, some browsers “sniff” the MIME type of a file to determine how to process it, even if the Content-Type is explicitly defined. This can be exploited to deliver malicious content.
- Mitigating Security Risks: Attackers could upload malicious files that are processed as legitimate scripts, leading to cross-site scripting (XSS) attacks or the execution of malicious code.
- Maintaining Content Integrity: Ensures that files are interpreted and rendered as intended by the server, preserving the integrity of the application.
Header Syntax
The only valid value for this header is nosniff, which tells the browser to strictly adhere to the declared Content-Type of the resource.
How Does X-Content-Type-Options Works?
When X-Content-Type-Options: nosniff is present in an HTTP response:
- The browser refuses to load stylesheets unless the Content-Type is text/CSS.
- The browser refuses to execute scripts unless the Content-Type is application/JavaScript.
For instance, If a server serves a .js file with Content-Type: text/plain and includes the nosniff directive, the browser will block the file from executing as a script.
How to Implement X-Content-Type-Options?
To implement X-Content-Type-Options: nosniff, configure your web server or application to include this header in all HTTP responses. Below are examples for common servers:
- Apache:
- Nginx:
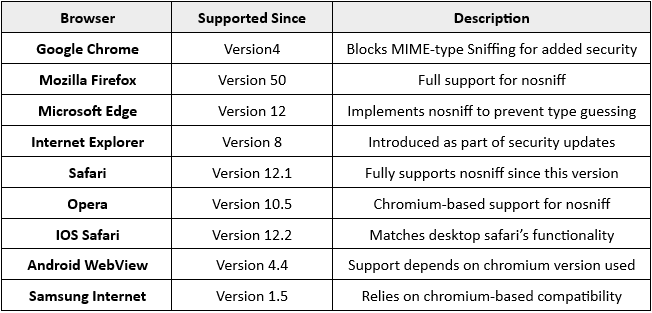
Compatibility
Conclusion
The X-Content-Type-Options header is a critical security measure to prevent MIME-type sniffing attacks. Proper implementation ensures that resources are processed only as intended, reducing vulnerabilities such as XSS. By configuring this header across your application, you enhance security and maintain the integrity of your content.
References
https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Content-Type-Options