What is X-XSS-Protection?
X-XSS-Protection is a HTTP header used to configure the Cross-Site Scripting (XSS) filter built into most modern web browsers. XSS filters aim to detect and mitigate certain types of XSS attacks by sanitizing malicious scripts injected into web pages. When properly configured, this header enhances the security of a web application by providing an additional layer of defence against XSS vulnerabilities.
What is Cross-Site Scripting (XSS)?
Cross-Site Scripting (XSS) is a type of security vulnerability that allows attackers to inject malicious scripts into web pages viewed by other users. These scripts can be used to steal sensitive data, hijack user sessions, or perform unauthorized actions on behalf of the victim. XSS attacks exploit the trust between users and the application, often targeting input fields, URLs, or stored data to deliver the malicious payload.
How Does X-XSS-Protection Work?
When a browser detects that a page is attempting to execute malicious scripts (e.g., scripts injected into a URL parameter), the XSS filter can:
- Sanitize the Script: The browser modifies the potentially malicious script to make it harmless.
- Block the Page: If sanitization is not possible, the browser may block the entire page from rendering.
X-XSS-Protection Directives:
The X-XSS-Protection header offers several configuration options, allowing developers to control how the browser’s XSS filter operates. These directives are:
- X-XSS-Protection:0
- Disables the XSS filter entirely. This option should only be used if the filter causes significant issues or false positives.
- X-XSS-Protection:1
- Enables the XSS filter. When a potential XSS attack is detected, the browser attempts to sanitize the malicious content and render the page safely.
- X-XSS-Protection:1; mode=block
- Enables the XSS filter and prevents the page from rendering if an attack is detected. This is a stronger option compared to 1, as it ensures that no potentially unsafe content is displayed.
- X-XSS-Protection:1; report=<reporting-URL>
- Enables the XSS filter and sends a report to the specified URL when a potential XSS attack is detected. This allows developers to log and analyse attack attempts.
Use Cases and Benefits
- Default Security: In older browsers, X-XSS-Protection can mitigate basic XSS attacks without requiring additional development.
- Layered Defence: Adds an extra layer of protection, complementing server-side and client-side validation.
- Attack Reporting: Provides insight into attempted XSS attacks when using the report directive.
How to Implement X-XSS-Protection
- Web Server Configuration:
- On Apache: Add the following line to your .htaccess file or Apache configuration:
- On Nginx: Add the following line to your nginx.conf or relevant site configuration:
- On Apache: Add the following line to your .htaccess file or Apache configuration:
- Application Code:
- In PHP:
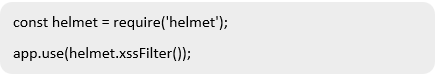
- In Express.js (Node.js): Use the helmet middleware:
- In PHP:
Limitations
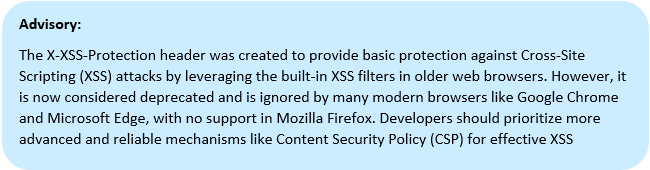
- Compatibility: Not all modern browsers fully support the X-XSS-Protection header. For example, it is ignored by newer versions of Google Chrome.
- Ineffectiveness Against Advanced Attacks: Advanced XSS techniques, such as those using browser-specific vulnerabilities, may bypass the filter.
- Potential False Positives: Legitimate functionality on a page may inadvertently trigger the XSS filter.
Best Practices
- Use in Combination with CSP: Complement X-XSS-Protection with Content Security Policy (CSP) for comprehensive XSS prevention.
- Set to “mode=block”: Use the mode=block directive to prevent rendering of malicious content.
- Avoid Overreliance: Do not rely solely on X-XSS-Protection; implement proper input validation and output encoding.
Alternatives and Future Directions
Given the deprecation of X-XSS-Protection in some browsers, web developers should prioritize robust XSS prevention strategies such as:
- Content Security Policy (CSP): Enforce strict rules for the execution of scripts and resources.
- Input Validation and Output Encoding: Sanitize user inputs and ensure proper encoding before displaying content.
Conclusion
While X-XSS-Protection is a useful security mechanism, its effectiveness is limited in modern web environments. Developers should use it as part of a layered security approach, incorporating other measures like CSP and secure coding practices to ensure comprehensive protection against XSS vulnerabilities.
References
https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-XSS-Protection